“Orchestrating Self-Evolving Agents with CrewAI and NVIDIA NemoClaw — CrewAI handles the coordination, NemoClaw handles the security. Neither does the other’s job.”
— CrewAI blog, official NemoClaw integration announcement, 2026
NemoClaw is NVIDIA’s enterprise security wrapper for agentic AI — the kernel-level sandboxed runtime that adds isolation, policy enforcement, and privacy routing to the open-source OpenClaw agent framework. CrewAI is the multi-agent orchestration framework that defines how multiple agents collaborate on complex tasks through role-based delegation, sequential and parallel execution patterns, and structured output passing between agents. When CrewAI published its official NemoClaw integration guide, it formalized a division of responsibility that enterprise teams had been improvising: CrewAI owns orchestration, NemoClaw owns security.
This article covers the technical integration path: installing the NeMo Agent Toolkit v1.5.0 that bridges CrewAI and NemoClaw, configuring supervisor-worker architectures where the supervisor delegates to sandboxed workers, implementing role-based security policies that restrict each agent to its designated tools and data, and the operational patterns that keep multi-agent workflows auditable and compliant.
For background on NemoClaw’s multi-agent security model, see our coverage of The AI Agent Stack in 2026. For the security contact to discuss enterprise multi-agent deployments, visit our Contact page.
The Multi-Agent Security Problem CrewAI Cannot Solve Alone
CrewAI is excellent at orchestration. It defines crews (groups of agents), assigns roles (researcher, writer, reviewer), sequences tasks, passes structured outputs between agents, and manages execution flow. What CrewAI does not provide is runtime security. CrewAI agents execute with the permissions of the host process. If the host process runs as root, every agent in the crew runs as root. If one agent is compromised through prompt injection, it can access the tools, files, and network connections of every other agent in the crew.
This is not a CrewAI bug — it is a design boundary. CrewAI is an orchestration framework, not a security runtime. The CrewAI team recognized this gap explicitly when they published the NemoClaw integration. Their blog post states the division clearly: “CrewAI handles orchestration, NemoClaw handles security.” The integration gives each CrewAI agent its own NemoClaw sandbox with independent filesystem, network, and tool access policies.
Consider a financial analysis crew with three agents: a data collector (accesses market APIs), a portfolio analyzer (reads client portfolio data), and a report writer (generates PDF reports). Without NemoClaw, all three agents share the same process permissions. A prompt injection attack against the data collector — which faces external, untrusted API responses — could pivot to the portfolio analyzer’s client data. With NemoClaw, each agent runs in an isolated sandbox. The data collector cannot see portfolio data. The report writer cannot call market APIs. Compromise of one agent does not compromise the crew.
Supervisor-Worker Architecture in NemoClaw + CrewAI
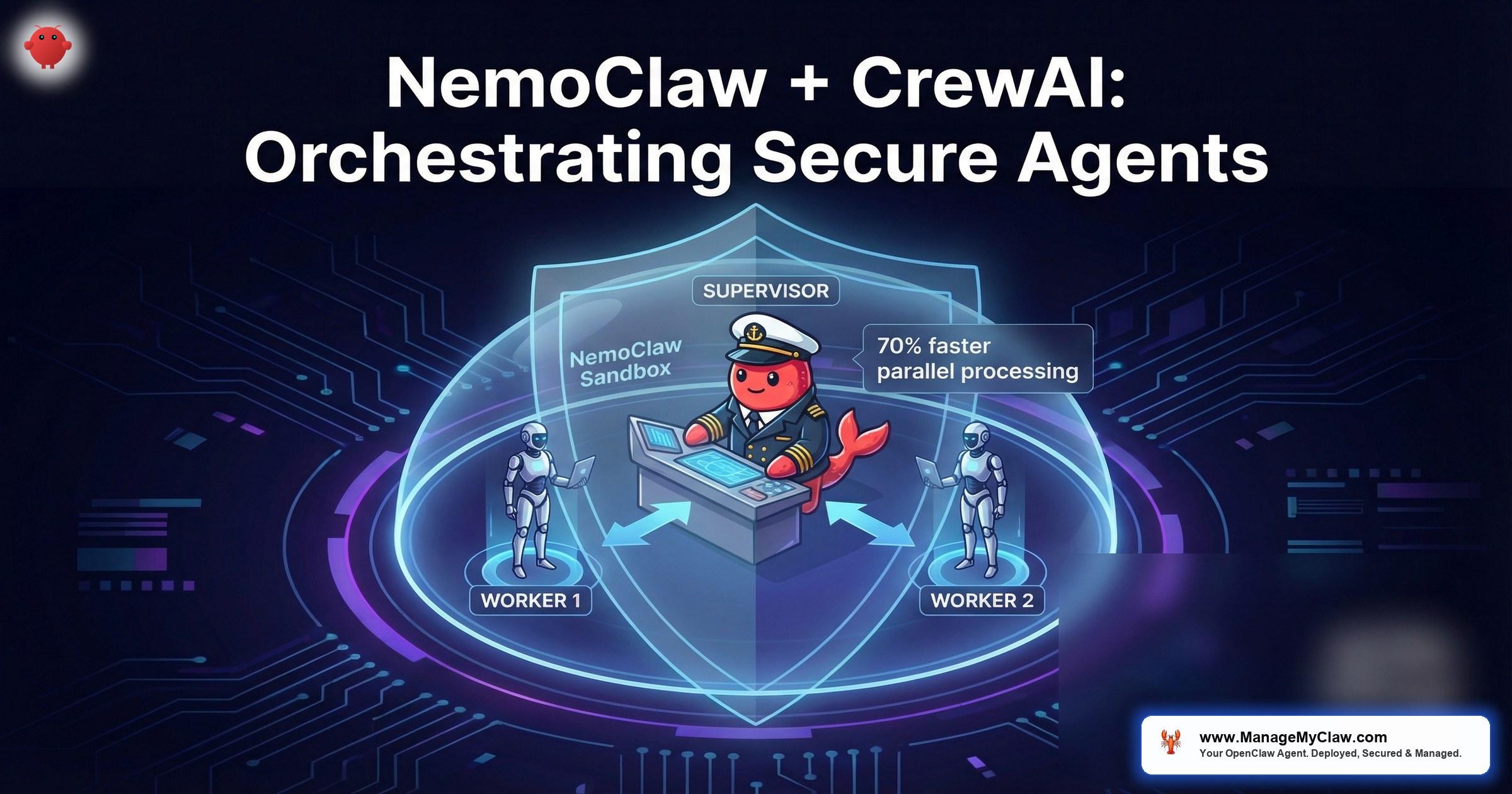
The NemoClaw + CrewAI integration uses a supervisor-worker pattern. The supervisor agent runs in a restricted NemoClaw sandbox with orchestration-only permissions — it can dispatch tasks to worker agents and receive their outputs, but it cannot directly access tools, filesystems, or network resources. Each Worker executes subtasks with specialized tools (code execution, database queries, web search, API calls) and returns structured results to the Supervisor. The Supervisor integrates outputs and dynamically spawns additional Workers or reprioritizes existing ones based on task progress and intermediate results.
This is a fundamental difference from the default CrewAI execution model. In default CrewAI, the “manager” agent (when using hierarchical process) runs in the same process space as every worker. In the NemoClaw integration, the supervisor communicates with workers through NemoClaw’s inter-sandbox messaging channel — a controlled IPC mechanism that passes structured data but does not share memory, file descriptors, or network sockets. NemoClaw’s OpenShell Runtime enforces every action at the infrastructure level, not within agent code — meaning security boundaries cannot be bypassed by the agent’s own reasoning or tool use.
| Component | CrewAI Responsibility | NemoClaw Responsibility |
|---|---|---|
| Task sequencing | Define task order, dependencies, outputs | No role — orchestration is CrewAI’s domain |
| Agent roles | Assign role descriptions, backstories, goals | Enforce role-specific sandbox policies |
| Tool access | Register tools with agents | Allow/deny tool execution per sandbox policy |
| Filesystem access | Not controlled | Landlock-enforced per-agent path restrictions |
| Network access | Not controlled | Namespace-isolated per-agent network policies |
| Inter-agent communication | Structured output passing between tasks | IPC channel with message validation |
| Kill switch | Not available | Immediate sandbox termination per agent |
Installing NeMo Agent Toolkit v1.5.0 with CrewAI
NeMo Agent Toolkit v1.5.0 is the release that added official CrewAI integration. The toolkit provides the bridge layer that translates CrewAI’s agent definitions into NemoClaw sandbox configurations. Each CrewAI agent is automatically wrapped in a NemoClaw sandbox at runtime — no changes to existing CrewAI code are required beyond swapping the execution backend.
Prerequisites
- NemoClaw installed and running (see our Implementation Guide)
- CrewAI 0.60+ installed (
pip install crewai) - Python 3.10+
- Linux with kernel 5.13+ (required for Landlock sandbox support)
# Install NeMo Agent Toolkit v1.5.0
$ pip install nemo-agent-toolkit==1.5.0
# Verify CrewAI integration is available
$ python -c "from nemo_agent_toolkit.integrations import crewai; print('CrewAI integration available')"
CrewAI integration available
# Verify NemoClaw connection
$ nemoclaw status
Status: RUNNING (sandboxed)
Agent Toolkit: v1.5.0
Integrations: crewai, langchain, autogenConfiguring a Secure Crew with Per-Agent Sandboxes
# crew_config.py — Financial analysis crew with NemoClaw sandboxing
from crewai import Agent, Task, Crew, Process
from nemo_agent_toolkit.integrations.crewai import NemoClawBackend
# Initialize the NemoClaw execution backend
backend = NemoClawBackend(
config_path="/etc/nemoclaw/crew-policies/",
sandbox_mode="deny-by-default",
inter_agent_ipc=True
)
# Each agent gets its own sandbox policy
data_collector = Agent(
role="Market Data Collector",
goal="Fetch current market data from approved APIs",
backstory="Senior data engineer with API integration expertise",
tools=[market_api_tool, csv_parser_tool],
nemoclaw_policy="data-collector.yaml" # NemoClaw extension
)
portfolio_analyzer = Agent(
role="Portfolio Analyzer",
goal="Analyze client portfolio against market conditions",
backstory="Quantitative analyst with 15 years experience",
tools=[portfolio_reader_tool, analysis_tool],
nemoclaw_policy="portfolio-analyzer.yaml"
)
report_writer = Agent(
role="Report Writer",
goal="Generate compliant PDF reports for client delivery",
backstory="Financial communications specialist",
tools=[pdf_generator_tool, template_tool],
nemoclaw_policy="report-writer.yaml"
)
# Crew uses hierarchical process with NemoClaw backend
financial_crew = Crew(
agents=[data_collector, portfolio_analyzer, report_writer],
tasks=[collect_task, analyze_task, report_task],
process=Process.hierarchical,
manager_llm="nemotron-3-super-12b",
execution_backend=backend # NemoClaw sandbox enforcement
)Per-Agent YAML Policy Files
agent: "data-collector"
sandbox:
mode: deny-by-default
filesystem:
read:
- "/tmp/market-data/"
write:
- "/tmp/market-data/output/"
network:
allowed_endpoints:
- "api.marketdata.com:443"
- "feeds.bloomberg.com:443"
deny_all_other: true
tools:
allowed:
- "market_api_tool"
- "csv_parser_tool"
denied:
- "*"agent: "portfolio-analyzer"
sandbox:
mode: deny-by-default
filesystem:
read:
- "/data/client-portfolios/"
- "/tmp/market-data/output/"
write:
- "/tmp/analysis-output/"
network:
deny_all: true
tools:
allowed:
- "portfolio_reader_tool"
- "analysis_tool"
denied:
- "*"The portfolio analyzer reads client data — names, account numbers, holdings, balances. This is the most sensitive data in the workflow. By setting network.deny_all: true, even a fully compromised portfolio analyzer agent cannot exfiltrate data. It can only write to /tmp/analysis-output/, which the report writer reads. The attack surface is reduced to the IPC channel, which NemoClaw validates for schema compliance.
Role-Based Collaboration Patterns for Secure Crews
CrewAI supports three process types: sequential (agents execute in order), hierarchical (a manager delegates to workers), and consensual (agents vote on next steps). Each maps to a different NemoClaw security topology.
Sequential Process: Pipeline Isolation
In a sequential crew, Agent A’s output becomes Agent B’s input. NemoClaw enforces this by granting Agent B read access only to Agent A’s designated output directory. Agent B cannot read Agent A’s working directory, intermediate files, or tool execution logs. The data flow is a one-way pipeline, enforced at the kernel level.
Hierarchical Process: Supervisor Sandboxing
The supervisor agent in a hierarchical crew needs special treatment. Its NemoClaw policy should allow IPC communication with all worker sandboxes but deny direct filesystem and network access. The supervisor delegates work — it should never execute tools itself. This prevents a prompt injection attack against the supervisor from directly accessing any resource; the attacker would need to compromise both the supervisor and a specific worker to reach the worker’s resources.
agent: "supervisor"
sandbox:
mode: deny-by-default
filesystem:
read: []
write: []
network:
deny_all: true
ipc:
allowed_targets:
- "data-collector"
- "portfolio-analyzer"
- "report-writer"
message_validation: strict
tools:
denied:
- "*"Monitoring, Logging, and Kill Switch Per Agent
Each NemoClaw sandbox produces an independent audit log. When a CrewAI crew has five agents, you get five separate audit streams — one per agent. This is intentional. Commingled audit logs make it impossible to attribute actions to specific agents during incident response. NemoClaw’s per-agent logging means you can reconstruct exactly which agent accessed which resource, at what time, and what the supervisor instructed it to do.
# View audit log for a specific agent in the crew
$ nemoclaw logs --agent data-collector --last 50
[2026-03-20 09:14:22] TOOL_CALL: market_api_tool (endpoint: api.marketdata.com)
[2026-03-20 09:14:23] NETWORK: ALLOWED → api.marketdata.com:443
[2026-03-20 09:14:25] FILE_WRITE: /tmp/market-data/output/sp500-2026-03-20.csv
[2026-03-20 09:14:25] TOOL_RETURN: market_api_tool (success, 2.1s)
# View denied actions (attempted policy violations)
$ nemoclaw logs --agent data-collector --filter denied
[2026-03-20 09:15:01] NETWORK: DENIED → exfil.attacker.com:443 (not in allowed_endpoints)
[2026-03-20 09:15:01] FILE_READ: DENIED → /data/client-portfolios/ (not in read policy)
# Kill a specific agent without stopping the crew
$ nemoclaw kill --agent portfolio-analyzer
Agent portfolio-analyzer terminated. Sandbox destroyed.
Crew status: data-collector (running), report-writer (waiting)The per-agent kill switch is critical for multi-agent security. In vanilla CrewAI, if one agent behaves anomalously, the only option is to kill the entire crew process. With NemoClaw, you can terminate a single compromised agent while the rest of the crew continues operating. The supervisor receives a notification that the agent was killed and can either reassign the task to a replacement agent or terminate the crew gracefully.
NemoClaw GitHub issue #387 tracks a feature request for CrewAI to receive a structured callback when NemoClaw kills an agent, rather than an unhandled exception. Currently, killing an agent mid-task causes CrewAI to throw a RuntimeError that the crew’s error handler must catch. The workaround is wrapping the crew kickoff in a try/except that checks for NemoClaw termination signals.
Self-Evolving Agents: What CrewAI’s Blog Post Actually Means
CrewAI’s official integration post is titled “Orchestrating Self-Evolving Agents with CrewAI and NVIDIA NemoClaw.” The “self-evolving” language refers to CrewAI’s ability for agents to modify their own tool selections and execution strategies based on task outcomes. An agent that fails a task can request additional tools, adjust its approach, or ask the supervisor for different instructions.
NemoClaw constrains this self-evolution to the boundaries defined in the agent’s policy file. An agent can request a tool it does not currently have, but if that tool is not in the tools.allowed list, NemoClaw will deny the request. The agent can adapt its strategy within its sandbox; it cannot expand its sandbox. This is the critical security property — adaptive behavior within fixed privilege boundaries.
For teams evaluating whether to allow tool self-selection, the conservative approach is to lock the tool list in the YAML policy and disable CrewAI’s tool delegation feature. The progressive approach is to allow tool delegation within the NemoClaw whitelist, so agents can select from approved tools but never request unapproved ones. The wrong approach is enabling unrestricted tool delegation without NemoClaw enforcement — this is equivalent to giving every agent root access.
Frequently Asked Questions
Does the NemoClaw integration work with CrewAI’s memory feature?
Yes, but each agent’s memory is isolated within its sandbox. CrewAI’s short-term memory (within a task) and long-term memory (across tasks) are stored in the agent’s designated write directory. Agent A cannot read Agent B’s memory store. Shared memory across agents is only possible through the IPC channel, which the supervisor mediates. This prevents memory poisoning attacks where a compromised agent writes malicious context into another agent’s memory.
Is NemoClaw’s Supervisor compatible with LangGraph as well as CrewAI?
Yes. NemoClaw’s Supervisor-Worker architecture is compatible with both LangGraph and CrewAI orchestration frameworks. If your team has existing LangGraph workflows, you can migrate them to NemoClaw without rewriting the orchestration logic — swap the execution backend and apply NemoClaw sandbox policies. The NeMo Agent Toolkit v1.5.0 includes integration modules for both frameworks. This means teams are not locked into a single orchestration choice; you can run CrewAI crews alongside LangGraph graphs under the same NemoClaw security umbrella.
Can I use CrewAI with NemoClaw without NeMo Agent Toolkit?
Technically, yes — you can run each CrewAI agent as a separate process inside individual NemoClaw sandboxes and manage the IPC yourself. But NeMo Agent Toolkit v1.5.0 handles the sandbox lifecycle, IPC channel setup, policy loading, and audit log routing automatically. Building this plumbing manually is error-prone and not recommended. The toolkit is the supported integration path, and it is what CrewAI’s official blog post documents.
What is the performance overhead of per-agent sandboxing?
Sandbox creation adds approximately 200–400ms per agent at crew startup. During execution, the overhead comes from Landlock filesystem checks (sub-millisecond per call), seccomp syscall filtering (negligible), and IPC message passing (1–5ms per message depending on payload size). For a typical crew of 3–5 agents running tasks that take seconds to minutes each, the sandbox overhead is less than 1% of total execution time. The overhead becomes noticeable only in crews with hundreds of agents making rapid sub-second tool calls.
How does this compare to running CrewAI agents in separate Docker containers?
Docker containers provide process and filesystem isolation but require significantly more resources per agent (each container needs its own Python runtime, dependencies, and memory allocation). NemoClaw sandboxes use Landlock and seccomp at the kernel level without separate container runtimes — all agents share the same Python process but with kernel-enforced isolation. Startup is 200ms vs 2–5 seconds for Docker. Memory overhead is negligible vs 200–500MB per container. For crews with more than 3 agents, NemoClaw sandboxing is materially more efficient.