“AI agents are becoming a critical part of enterprise infrastructure. But without embedded security, they become the largest unmonitored attack surface in your environment.”
— CrowdStrike, Secure-by-Design AI Blueprint, GTC 2026
CrowdStrike’s 2026 Global Threat Report documented an 89% year-over-year increase in AI-enabled attacks. A Dark Reading poll found that 48% of cybersecurity professionals now rank agentic AI as the #1 attack vector heading into 2026. A Teleport survey from February 2026 reported that 88% of enterprises have already experienced AI agent security incidents. These aren’t projections. They’re the current state of the field.
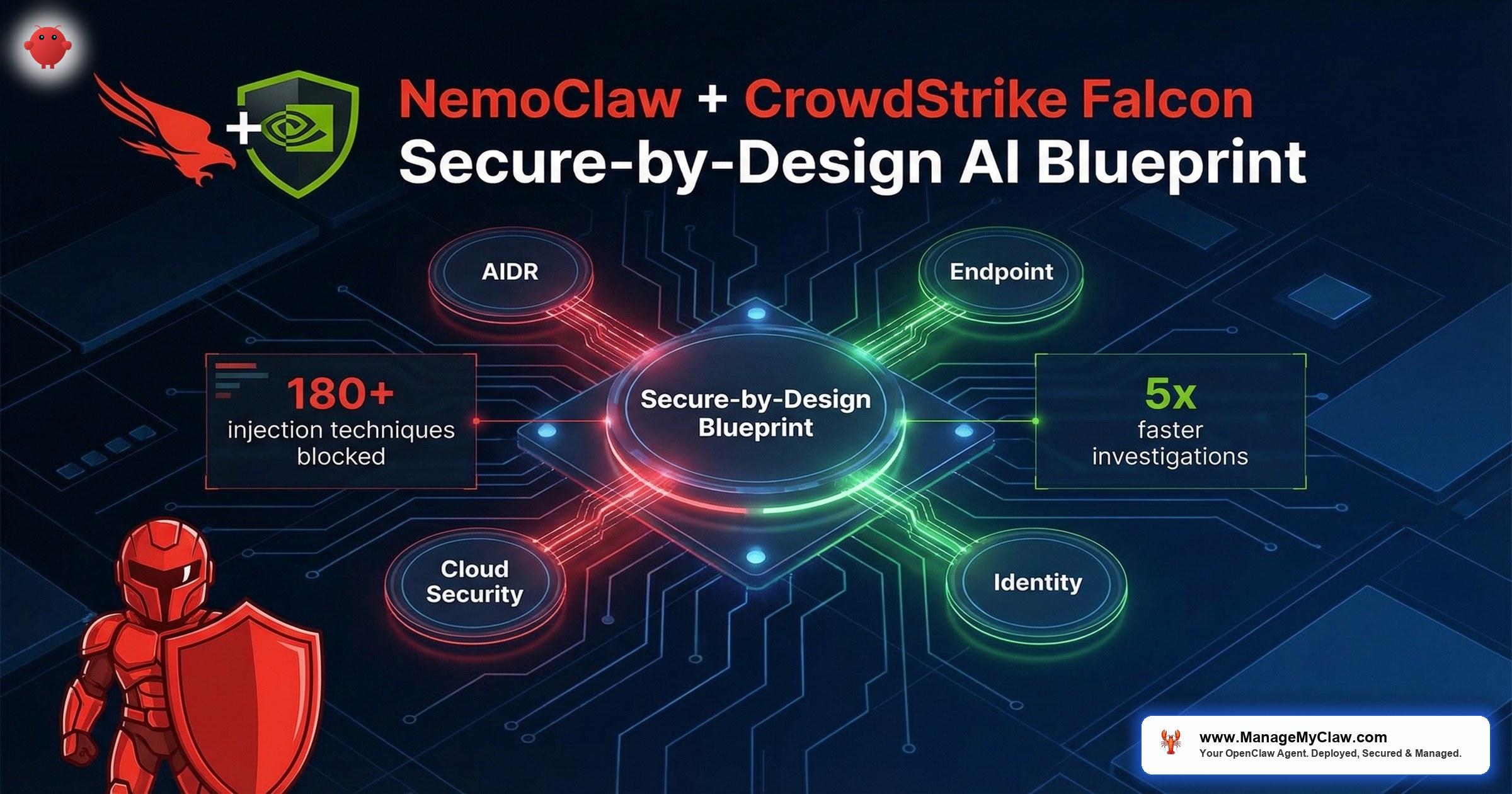
At GTC 2026, CrowdStrike and NVIDIA responded by unveiling the Secure-by-Design AI Blueprint — a reference architecture that integrates the CrowdStrike Falcon platform directly into NVIDIA’s OpenShell runtime. Not bolted on after deployment. Not layered on top of an existing stack. Embedded at the foundation of how autonomous AI agents are built, deployed, and governed.
This post breaks down the architecture: what each Falcon component does, how it maps to the NemoClaw security stack, which OWASP Agentic Top 10 risks it addresses, and what it means for enterprises planning production AI agent deployments in 2026.
of enterprises had AI agent security incidents (Teleport, Feb 2026)
YoY increase in AI-enabled attacks (CrowdStrike 2026 GTR)
Why “Bolt-On” Security Fails for Autonomous Agents
Traditional enterprise security follows a familiar pattern: deploy the application, then wrap it in firewalls, endpoint protection, and monitoring. That model works for deterministic software that behaves predictably. AI agents break it. They make autonomous decisions. They chain tool calls. They interact with APIs, filesystems, email systems, and databases based on inference — not hardcoded logic. The attack surface isn’t a static set of endpoints. It’s every decision the agent makes, every tool it invokes, and every data path it traverses.
The OWASP Top 10 for Agentic Applications (2026) codifies these risks. ASI02 (Tool Misuse) covers agents using available tools beyond intended scope. ASI03 (Identity & Privilege Abuse) covers agents inheriting overly broad credentials. ASI10 (Rogue Agents) covers agents that pass initial checks and then deviate from expected behavior. Each of these categories describes a failure mode that traditional perimeter security doesn’t address — because the threat isn’t coming from outside the network. It’s coming from inside the agent.
- ASI02 — Tool Misuse — An agent with unrestricted tool access can execute shell commands, send emails, or modify files beyond its intended scope
- ASI03 — Identity Abuse — Agents inheriting broad service accounts or static API tokens can access resources far beyond their task requirements
- ASI10 — Rogue Agents — Agents that pass initial validation can drift or be manipulated into exfiltrating data, escalating privileges, or taking destructive actions
The OWASP framework’s foundational concept — the Principle of Least Agency — captures the core problem. AI agents should be given the minimum autonomy, tool access, and credential scope required for their task. No more. Every excess capability is attack surface you carry for no operational benefit. But enforcing least agency requires security controls that understand agent behavior, not just network traffic. That’s what the CrowdStrike-NVIDIA blueprint is designed to provide.
Consider the difference: a firewall can block port 443 traffic to unauthorized domains. But it can’t determine whether the agent’s decision to call your CRM API was a legitimate workflow step or a prompt-injected exfiltration attempt. That distinction requires security that operates at the agent layer, not the network layer.
The Secure-by-Design AI Blueprint: Architecture Overview
The CrowdStrike-NVIDIA Secure-by-Design AI Blueprint isn’t a single product. It’s a reference architecture that maps CrowdStrike Falcon platform capabilities to specific layers of the NemoClaw security stack. The key architectural decision: security is embedded at the foundation of autonomous systems, not applied as a post-deployment overlay.
NemoClaw provides the runtime security substrate — OpenShell’s kernel-level sandbox, the YAML policy engine, and the privacy router. CrowdStrike Falcon adds the threat intelligence, identity governance, and detection-and-response capabilities that enterprises require for production deployment. Together, they address a problem that neither platform solves alone: governing autonomous AI agents with the same rigor applied to human users and traditional workloads.
Here’s how the components map:
| CrowdStrike Falcon Component | NemoClaw Layer | What It Secures | OWASP ASI Coverage |
|---|---|---|---|
| Falcon AI Detection & Response (AIDR) | OpenShell runtime | Every prompt, response, and agent action — real-time behavioral monitoring | ASI02, ASI10 |
| Falcon Next-Gen Identity Security | Policy engine + privacy router | Dynamic identity management for agents, access controls across data/APIs/services | ASI03 |
| Falcon Next-Gen MDR | Audit trail + SIEM integration | Managed detection and response with 5x investigation acceleration via NVIDIA AI | ASI09, ASI10 |
| Falcon MCP Connector | Agent tool layer | AI agent-to-Falcon integration for automated security analysis and threat hunting | ASI02, ASI03 |
| JetPatch Enterprise Control Plane | Governance layer | Operational governance — turns agents into governed corporate assets with lifecycle management | ASI10 |
Each of these components operates outside the agent’s own process. That’s the architectural distinction that makes the blueprint meaningful for enterprise security teams. Internal guardrails — system prompts, instruction files, application-layer validation — live inside the agent. A compromised or prompt-injected agent can potentially override them. The Falcon-NemoClaw integration enforces security at the OS, identity, and network layers, where the agent can’t reach.
4 Enforcement Points Across the OpenShell Stack
VentureBeat’s analysis of the blueprint identified 4 distinct enforcement points where Falcon embeds into the NemoClaw/OpenShell architecture. This is not a single integration point — it is security at every layer of the agent execution stack:
| Enforcement Point | Falcon Component | What It Secures |
|---|---|---|
| 1. Prompt-Response-Action Layer | Falcon AIDR | Monitors and secures every prompt, model response, and agent action in real time. Blocks prompt injection, jailbreaks, and credential leakage at the interaction layer. |
| 2. Hardware / Endpoint | Falcon Endpoint | Host-level controls and continuous behavioral monitoring across system activity and agent execution on DGX Spark and DGX Station hardware. |
| 3. Cloud Infrastructure | Falcon Cloud Security | Secures the AI-Q Blueprint cloud infrastructure — the orchestration layer that coordinates multi-agent workflows across distributed GPU resources. |
| 4. Agent Identity Boundaries | Falcon Identity | Enforces privilege boundaries for AI agents — per-task credential scoping, access governance, and identity lifecycle management. |
“Nvidia’s agentic AI stack is the first major platform to ship with security at launch, but governance gaps remain.”
— VentureBeat, Analysis of the Secure-by-Design AI Blueprint, March 2026
The VentureBeat observation is worth internalizing: shipping with security at launch is a meaningful first, but governance — the organizational policies, compliance documentation, and operational processes that translate security controls into auditable compliance posture — remains the responsibility of the deploying organization. The blueprint gives you the architecture. ManageMyClaw provides the governance implementation.
Falcon AI Detection & Response: Securing Every Agent Action
Falcon AIDR (AI Detection and Response) reached general availability on December 15, 2025, when CrowdStrike announced that it “extends the Falcon platform to secure the AI prompt and agent interaction layer.” AIDR is the real-time monitoring layer. It integrates directly into NVIDIA OpenShell to secure every prompt, every response, and every agent action. Unlike traditional endpoint detection that monitors file operations and process execution, AIDR understands agent behavior — the chain of tool calls, the reasoning patterns, the data flows between prompts.
AIDR’s prompt injection defense is powered by intelligence from 180+ known prompt injection and jailbreak techniques. It does not rely on static pattern matching — the detection engine is continuously updated with new adversarial techniques as they emerge in the wild. When your agent receives a prompt that attempts tool misuse (ASI02) — say, a seemingly legitimate instruction that chains 3 API calls to exfiltrate customer data to an unauthorized endpoint — AIDR detects the behavioral anomaly at the action level, not just the network level. The detection happens before the data leaves the sandbox, not after it hits your SIEM as a post-incident log entry.
known prompt injection & jailbreak techniques blocked by Falcon AIDR
AIDR Relationship Mapping: Full Runtime Visibility
AIDR does more than detect individual anomalies — it maps relationships between users, prompts, models, agents, and MCP servers across the entire runtime environment. This relationship graph captures who initiated which prompt, which model processed it, which agent acted on the output, and which MCP servers were invoked. Runtime logs are captured for compliance investigations and forensic analysis, giving your SOC team the full causal chain from user request to agent action.
AIDR also provides automatic credential and regulated data blocking — detecting and blocking credentials, API keys, and regulated data (PII, PHI, financial records) before they reach models or agents. If a prompt inadvertently contains a database password or a patient SSN, AIDR intercepts it at the prompt layer before the model ever processes it.
“The Secure-by-Design AI Blueprint embeds CrowdStrike Falcon directly into the NVIDIA AI stack — securing every prompt, response, and agent action to protect AI workloads from development to deployment.”
— CrowdStrike Press Release, GTC 2026
For CISOs, AIDR addresses a specific blind spot: the gap between “the agent is running inside a sandbox” and “we can see what the agent is doing inside that sandbox.” NemoClaw’s OpenShell sandbox provides the isolation boundary. AIDR provides the visibility into what happens within it. Isolation without visibility is a black box. Visibility without isolation is a monitoring-only posture. The blueprint delivers both.
An agent sandbox without behavioral monitoring is a locked room with no security cameras. You’ll know something went wrong when the room is empty. With AIDR, you see the agent reaching for the wrong shelf before it pulls anything off.
Falcon Next-Gen Identity Security: Agent Identity as a First-Class Primitive
The identity problem for AI agents is fundamentally different from the identity problem for human users. A human authenticates once, gets a session, and makes decisions within that session’s permission scope. An AI agent might authenticate with 5 different services, chain 12 API calls across 3 departments, and escalate its own privileges by requesting additional tool access — all within a single task execution. Traditional IAM systems weren’t built for this pattern.
Falcon Next-Gen Identity Security brings dynamic identity management for AI agents: scoped credentials that match the specific task, access controls that span data, APIs, and services, and identity lifecycle management that treats each agent instance as a governed entity — not a shared service account with a static API key.
- Per-task credential scoping — Each agent task receives credentials limited to the specific resources it needs, revoked on task completion
- Cross-service access governance — Access controls enforced across data stores, API endpoints, and third-party services in a unified policy
- Agent identity lifecycle — Creation, rotation, suspension, and revocation of agent identities managed as corporate assets, not developer shortcuts
- Privilege escalation detection — Real-time monitoring for agents requesting or obtaining access beyond their defined scope
This directly addresses OWASP ASI03 (Identity & Privilege Abuse). The Teleport survey found that 88% of enterprises have experienced AI agent security incidents — and identity abuse is a leading category. Agents running with broad service accounts, plaintext API tokens, or inherited developer credentials represent the same risk pattern that privilege escalation attacks exploit in human-user environments. The difference is that agents operate faster, chain more actions, and don’t hesitate before accessing something they shouldn’t.
NemoClaw’s YAML policy engine defines what an agent can access. Falcon Identity Security enforces who the agent is and whether that identity is authorized for the requested action. The combination creates a two-layer identity model: policy-level restrictions on the agent class and identity-level restrictions on the agent instance.
Falcon Endpoint: Behavioral Monitoring at the Hardware Layer
Falcon Endpoint extends identity and behavioral enforcement to the physical hardware layer. On DGX Spark and DGX Station deployments, Falcon Endpoint enforces host-level controls and continuous behavioral monitoring across system activity and agent execution. This is the enforcement layer that traditional cloud-native security tools cannot provide: visibility into GPU utilization patterns, process execution on the DGX host, and system-level activity that could indicate agent compromise or lateral movement.
For enterprises running local Nemotron inference on DGX hardware, this is a critical gap the blueprint fills. The privacy router ensures sensitive data stays on-premises. Falcon Endpoint ensures the on-premises hardware itself is monitored for compromise. Without both, you have data sovereignty but no assurance that the local environment is secure.
of cybersecurity professionals rank agentic AI as #1 attack vector (Dark Reading, 2026)
Falcon MDR and the MCP Connector: Investigation at Machine Speed
Falcon Next-Gen MDR (Managed Detection and Response) accelerates security investigations by integrating NVIDIA AI directly into the analysis pipeline. CrowdStrike reports 5x investigation acceleration when MDR analysts leverage the NVIDIA AI-powered workflow — compressing hours-long investigation cycles into minutes by automating log correlation, threat pattern matching, and remediation recommendation generation across the full AIDR relationship graph. For enterprise SOC teams managing dozens of AI agents across multiple departments, investigation speed isn’t a nice-to-have. It’s the difference between a contained incident and a breach.
Average eCrime breakout time — the window between initial compromise and lateral movement — fell to 29 minutes in CrowdStrike’s 2026 threat data. The fastest observed breakout was 27 seconds. When your AI agents are the attack vector, and the adversary moves in under 30 seconds, your detection and investigation capability needs to operate at a fundamentally different speed than traditional ticketing workflows.
The Falcon MCP Connector (github.com/CrowdStrike/falcon-mcp) adds another dimension: it connects AI agents directly to the Falcon platform for automated security analysis and threat hunting. This creates a feedback loop where security agents can query the Falcon platform for threat intelligence, correlate agent behavior against known attack patterns, and trigger automated response actions — all through the Model Context Protocol (MCP) standard.
CrowdStrike’s 2026 Global Threat Report: average eCrime breakout time is 29 minutes. Fastest observed: 27 seconds. When an AI agent is compromised, traditional incident response workflows that take hours to triage are already too slow. MDR with NVIDIA AI integration compresses that timeline by 5x — from hours to minutes.
For OWASP ASI10 (Rogue Agents), this combination is particularly relevant. A rogue agent may pass initial validation — correct credentials, approved tool access, expected behavior patterns — and then gradually deviate. MDR provides the continuous monitoring capability to detect that drift. The MCP connector provides the automated investigation capability to diagnose it before the 29-minute breakout window closes.
JetPatch Enterprise Control Plane: From Agents to Governed Assets
The Falcon components secure individual agent actions and identities. The JetPatch Enterprise Control Plane addresses the organizational layer: operational governance that turns “agents” into governed corporate assets. For enterprises deploying 10, 50, or 200 AI agents across multiple departments, the governance challenge extends beyond security into lifecycle management, compliance reporting, and operational accountability.
JetPatch’s control plane provides centralized visibility and management for NemoClaw deployments: which agents are running, what policies govern them, which departments own them, and what their compliance status is. It maps to the same governance model enterprises use for fleet management of servers, containers, and cloud workloads — applied to AI agents.
This is the layer that makes the difference between “we have AI agents” and “we have governed AI agents that our compliance team can audit.” EU AI Act reaches full enforcement in August 2026. SOC2 auditors are already asking about AI agent governance. The control plane provides the documentation, the audit trail, and the centralized policy management that those requirements demand.
Think of JetPatch as the difference between a fleet of company vehicles and a managed fleet of company vehicles. Both get you from point A to point B. Only one has GPS tracking, maintenance schedules, driver logs, insurance documentation, and a central dashboard that tells the CFO exactly what each vehicle costs per mile.
How the Blueprint Maps to OWASP Agentic Top 10 Risks
The OWASP Agentic Top 10 provides the risk taxonomy. The CrowdStrike-NemoClaw blueprint provides the control mapping. Here’s how the architecture addresses the 3 most critical risk categories for enterprise deployments:
ASI02: Tool Misuse & Exploitation
The risk: Agents use available tools in ways that exceed intended scope — executing shell commands, accessing restricted filesystems, calling unauthorized APIs. This happens through prompt injection, goal hijacking, or simply overly broad tool permissions.
Blueprint controls: NemoClaw’s OpenShell policy engine restricts tool access at the binary, destination, method, and path level — enforced at the OS layer, not the application layer. Falcon AIDR monitors the behavioral pattern of tool usage in real time. If an agent’s tool call sequence deviates from established baselines, AIDR flags the anomaly before the action completes. The Falcon MCP connector enables security agents to cross-reference tool usage patterns against CrowdStrike’s threat intelligence database.
ASI03: Identity & Privilege Abuse
The risk: Agents inherit overly broad credentials. Service accounts with admin-level access. Static API tokens stored in environment files. Credentials that don’t expire, don’t rotate, and grant access to resources the agent never needs to touch.
Blueprint controls: Falcon Next-Gen Identity Security applies dynamic, per-task credential scoping to agent identities. Each agent instance receives only the credentials required for its specific task. Access controls span data, APIs, and services in a unified governance model. NemoClaw’s privacy router adds a data-level control: sensitive data stays on local Nemotron models and never reaches external APIs, regardless of the agent’s credential scope.
ASI10: Rogue Agents
The risk: Agents pass initial checks — valid credentials, approved tool access, expected behavior — and then deviate. This can result from adversarial manipulation, model drift, or exploited vulnerabilities in the agent’s reasoning chain.
Blueprint controls: AIDR provides continuous behavioral monitoring that extends beyond initial validation. Falcon MDR delivers the investigation capability to diagnose deviations. JetPatch’s control plane provides the governance framework to track agent state across the fleet. NemoClaw’s OpenShell sandbox ensures that even a rogue agent’s blast radius is contained within its isolation boundary — it can break things inside the sandbox without reaching the host system or other agents.
2026
89% YoY increase in AI-enabled attacks (CrowdStrike 2026 GTR). 88% of enterprises have had AI agent security incidents (Teleport). 48% of CISOs rank agentic AI as the #1 attack vector (Dark Reading). Average eCrime breakout time: 29 minutes.
The Secure-by-Design Blueprint exists because the threat data left no room for “we’ll add security later.” Every major security vendor is publishing agentic AI governance frameworks in the same quarter. That’s not a trend. That’s an industry acknowledging a gap it can no longer ignore.
The Full Stack: 5 Layers of Agent Security
When the Falcon components integrate with NemoClaw’s security stack, the combined architecture provides defense in depth across 5 distinct layers. Each layer addresses a different failure mode. No single layer is sufficient on its own — the value is in the combination.
| Layer | Technology | What It Prevents |
|---|---|---|
| 1. Isolation | OpenShell kernel-level sandbox (Landlock, seccomp, network namespaces) | Container escape, host system compromise, lateral movement between agents |
| 2. Policy | NemoClaw YAML policy engine (binary, destination, method, path) | Unauthorized tool execution, unapproved network access, filesystem violations |
| 3. Identity | Falcon Next-Gen Identity Security + privacy router | Credential abuse, privilege escalation, unauthorized data access |
| 4. Detection | Falcon AIDR + Falcon MCP Connector | Behavioral anomalies, prompt injection, tool misuse, rogue agent drift |
| 5. Response | Falcon Next-Gen MDR + JetPatch Control Plane | Investigation delays, uncoordinated response, governance gaps, compliance drift |
This layered model follows the Principle of Least Agency at every tier. The sandbox restricts the agent’s operational boundary. The policy engine restricts what the agent can do within that boundary. Identity security restricts who the agent can be and what it can access. Detection catches deviations the policy engine didn’t anticipate. Response ensures deviations are investigated and contained before the breakout window closes.
The OWASP Agentic Top 10’s foundational concept: minimum autonomy, minimum tool access, minimum credential scope for every agent task. The 5-layer architecture enforces this principle at the OS level (sandbox), the application level (policy engine), the identity level (Falcon), the behavioral level (AIDR), and the organizational level (JetPatch). No single layer depends on the agent’s cooperation.
Enterprise Implementation: What the Blueprint Requires
The Secure-by-Design Blueprint is a reference architecture, not a turnkey product. Deploying it in a production enterprise environment requires integration work across multiple systems. Here’s what security teams should plan for:
Blueprint deployment prerequisites
- NVIDIA GPU infrastructure — NemoClaw’s privacy router requires local GPU compute for Nemotron model inference. Minimum: 4 vCPU, 8GB RAM, NVIDIA GPU.
- CrowdStrike Falcon platform — Active Falcon subscription with AIDR, Identity Security, and MDR modules
- NemoClaw stack deployment — OpenShell sandbox + YAML policy engine + privacy router configured for your environment
- SIEM integration — Falcon and NemoClaw audit trails routed to your existing SIEM/SOC infrastructure
- Identity provider integration — Falcon Identity Security connected to your corporate IdP for agent credential management
- Policy engineering — Custom YAML policies that map to your organization’s security posture, compliance requirements, and data classification
NemoClaw installs in a single command. Configuring it for production — kernel-level sandbox policies, privacy routing tables, Falcon integration, compliance documentation, multi-agent governance — is specialist work that typically takes 2–6 weeks depending on scope. The policy engineering alone requires understanding of your organization’s data flows, agent use cases, and compliance requirements. The YAML policy engine supports 4-level evaluation (binary, destination, method, path), and each agent workflow needs policies configured at all 4 levels.
A note on maturity: NemoClaw is alpha/early-access software as of March 2026. The core security primitives — OpenShell sandbox, policy engine, privacy router — work today and have been validated by 17 NVIDIA launch partners including Adobe, Salesforce, SAP, and CrowdStrike. Enterprise organizations deploying now are building governance infrastructure ahead of general availability. Organizations that wait for GA will be 6–12 months behind on policy engineering, team training, and compliance documentation.
NVIDIA launch partners validating NemoClaw — Adobe, Salesforce, SAP, CrowdStrike, ServiceNow, Red Hat, and more
CISO Evaluation Framework: 7 Questions for Your Security Review
If your organization is evaluating the Secure-by-Design Blueprint — or any AI agent security architecture — these are the questions your security review should answer:
- Where does enforcement live? Inside the agent (system prompt, application layer) or outside the agent (OS, kernel, identity provider)? The blueprint enforces outside. Internal-only enforcement is a suggestion the agent can override.
- How are agent identities managed? Static API keys in .env files? Shared service accounts? Or per-task, scoped, rotatable credentials with lifecycle governance? Falcon Identity Security provides the latter.
- What happens between initial validation and task completion? Is there continuous behavioral monitoring (AIDR), or does the agent operate unwatched after authentication?
- What’s your investigation timeline? If an agent deviates, how quickly can your SOC detect, investigate, and contain? With a 29-minute average breakout time, traditional ticketing workflows are too slow.
- Can you audit agent activity for compliance? SOC2, HIPAA, EU AI Act (August 2026) all require audit trails. Does your architecture produce the evidence your compliance team needs?
- How do you govern the fleet? One agent is a project. Fifty agents across 8 departments is a governance challenge. Do you have centralized visibility, policy management, and lifecycle controls?
- What’s the blast radius of a compromised agent? If Agent A is compromised, can it reach Agent B’s data? Can it access the host system? Can it move laterally? Kernel-level sandbox isolation defines the answer.
The Secure-by-Design Blueprint provides an architecture that addresses each of these questions. ManageMyClaw provides the implementation — deploying the NemoClaw stack, configuring Falcon integration, building the YAML policies, and producing the compliance documentation. The Assessment tier ($2,500) delivers an architecture review, OWASP ASI mapping, and a written remediation plan before any implementation commitment.
Frequently Asked Questions
Does the Secure-by-Design Blueprint require CrowdStrike Falcon?
The blueprint is designed around the Falcon platform. NemoClaw’s core security stack (OpenShell sandbox, policy engine, privacy router) works independently, but the detection, identity, and MDR layers are Falcon-specific. If your organization uses a different endpoint platform, the NemoClaw layers still apply — but the Falcon integration components require an active Falcon subscription. ManageMyClaw can integrate NemoClaw with your existing SIEM/SOC infrastructure regardless of endpoint vendor.
How does NemoClaw + Falcon compare to deploying OpenClaw with Docker hardening?
Docker hardening (cap-drop=ALL, read-only root, seccomp profiles) provides container-level isolation. NemoClaw’s OpenShell adds kernel-level enforcement (Landlock, seccomp, network namespaces) that operates below the container runtime. Falcon adds behavioral monitoring, identity governance, and managed detection that Docker has no equivalent for. The gap is the difference between “the container is locked” and “we know what’s happening inside the container, who’s accessing it, and we can investigate anomalies in minutes.” See our sandboxing comparison for the full isolation spectrum.
What does “alpha/early-access” mean for enterprise deployment risk?
NemoClaw’s core security primitives work today. 17 enterprise partners — including Adobe, Salesforce, SAP, and CrowdStrike — are building on the platform. Alpha means the API surface may change, new capabilities are being added, and documentation is evolving. The architecture is stable. The governance patterns you build now (policies, compliance documentation, team training) carry forward to GA. The risk of waiting is larger: organizations that deploy at GA without existing governance infrastructure will be 6–12 months behind.
What OWASP Agentic Top 10 categories does the blueprint NOT address?
The blueprint provides strong coverage for ASI02 (Tool Misuse), ASI03 (Identity Abuse), ASI09 (Human-Agent Trust), and ASI10 (Rogue Agents). ASI01 (Goal Hijacking) requires application-layer defenses (prompt engineering, instruction isolation) in addition to the infrastructure controls. ASI04–ASI08 (data leakage, supply chain, unexpected code execution, denial of service, input manipulation) receive partial coverage through sandbox isolation and policy enforcement, but require additional controls. See our full OWASP Agentic Top 10 mapping.
Can we start with a pilot before committing to full implementation?
Yes. ManageMyClaw’s Pilot Program ($5,000 for 30 days) deploys a fully hardened NemoClaw stack with 1 agent and 1 workflow. The pilot includes CrowdStrike Falcon integration if your organization is a Falcon customer. Written evaluation at Day 30 with go/no-go recommendation and TCO projection. Pilot cost credits toward full implementation if approved.
What’s the Falcon MCP Connector and do we need it?
The Falcon MCP Connector (open source on GitHub) connects AI agents to the Falcon platform via the Model Context Protocol standard. It enables agents to perform automated security analysis and threat hunting through Falcon’s APIs. It’s most valuable for security teams that want their own AI agents to participate in incident investigation and threat correlation. For most initial deployments, AIDR and Identity Security provide the critical controls. The MCP Connector adds operational automation on top.
Our Assessment tier ($2,500) delivers an architecture review, OWASP ASI mapping, Falcon integration assessment, and written remediation plan. 1-week turnaround. No implementation commitment required.
Schedule Architecture Review