“One agent is manageable. Ten agents need governance. A hundred agents need a control plane. Without centralized lifecycle management, enterprise AI agent deployments become ungovernable within months.”
— JetPatch Enterprise Control Plane for NemoClaw announcement, PRNewswire, March 2026
Gartner projects 40% of enterprise applications will include AI agents by end of 2026. For most enterprises, the question is no longer whether to deploy autonomous agents but how to govern them at scale. NemoClaw solves the security problem — kernel-level sandbox, YAML policy engine, privacy router. But security is only half the governance equation. When an enterprise runs 10, 50, or 200 agents across multiple departments, someone needs to answer operational questions that NemoClaw was not designed to address: Which agents are running? Are all agents on the same policy version? Which agent consumed $12,000 in API costs last month? Is the marketing department’s agent compliant with the same standards as the finance department’s agent?
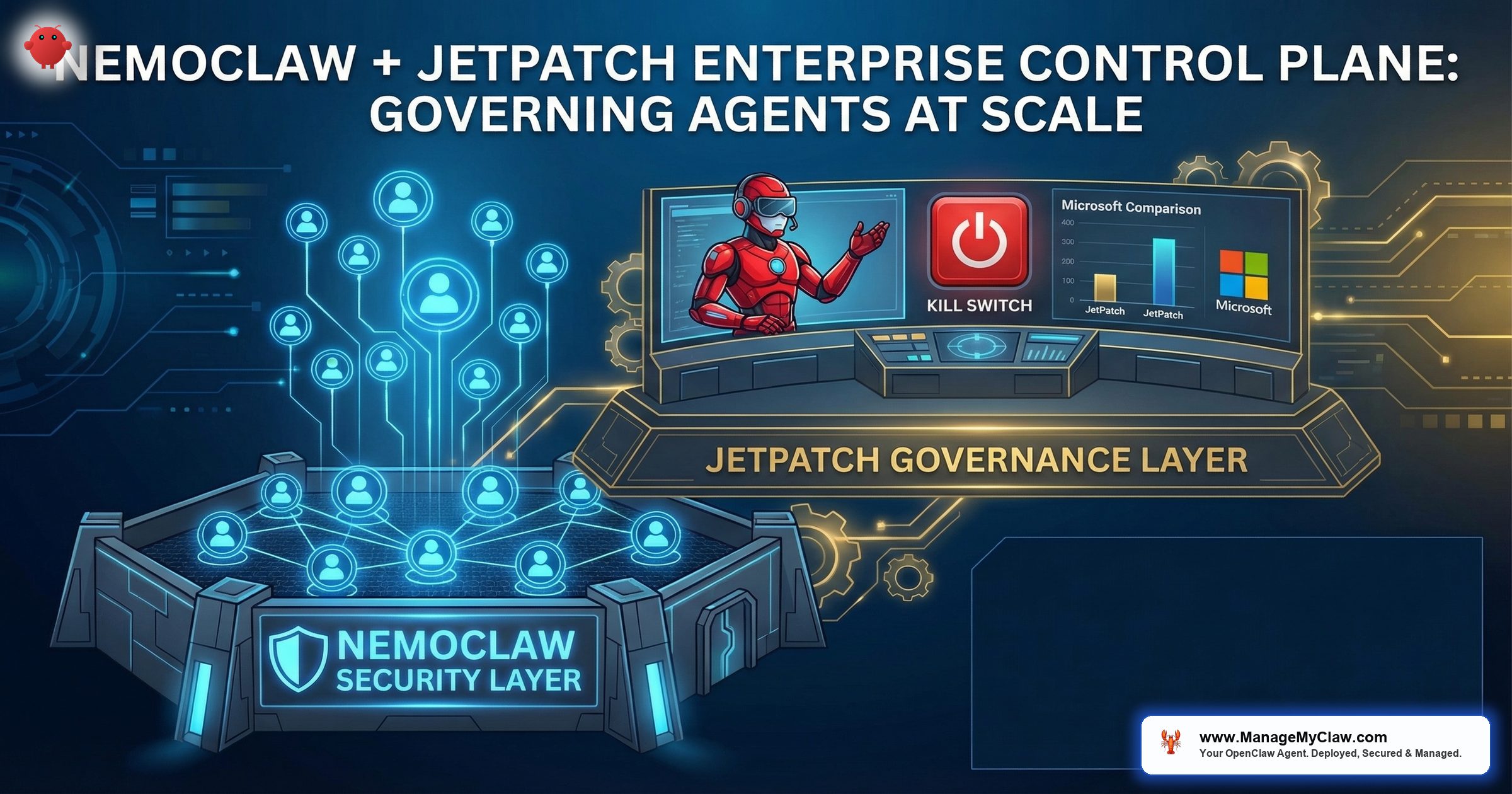
JetPatch announced their Enterprise Control Plane for NemoClaw on March 18, 2026 — just two days after the GTC NemoClaw launch (PRNewswire) — and it addresses this exact gap. The control plane sits on top of NemoClaw’s security layer and provides the operational governance that enterprise IT teams need: lifecycle management, centralized policy distribution, compliance reporting, fleet management, and cost allocation. Two headline capabilities: kill-switch integration to instantly pause or suspend autonomous agent processes across global infrastructure, and declarative policy governance to centrally manage and enforce OpenShell security sandboxes so agents cannot operate outside defined inference boundaries (PRNewswire, VMblog). JetPatch works alongside CrowdStrike Falcon, connecting agent operations with broader enterprise security workflows. NemoClaw keeps each agent secure. JetPatch keeps the fleet of agents governed.
JetPatch’s NemoClaw integration is available now for early-access customers in financial services, healthcare, and government verticals (PRNewswire). These are the sectors with the strictest regulatory requirements — SOC2, HIPAA, FedRAMP — and the greatest immediate need for centralized agent governance. General availability timeline has not been announced.
This post breaks down what the Enterprise Control Plane does, how it layers on top of NemoClaw’s architecture (covered in our Architecture Deep Dive), and how it compares to Microsoft’s Agent Governance Toolkit. For implementation details, see our NemoClaw Implementation Guide.
of enterprise apps will include AI agents by end 2026 (Gartner)
agentic AI enterprise market in 2026
Why Security Is Not Governance: The 1-to-N Agent Problem
A single NemoClaw agent is manageable. An engineer configures the YAML policy, a security team reviews it, the agent deploys into a sandboxed environment, and operations monitors the audit logs. The workflow is linear and the blast radius of any misconfiguration is contained to one agent.
Enterprise deployments are not single-agent. They are multi-agent fleets. Consider a mid-market company with 200 employees deploying NemoClaw across 5 departments:
- Customer Support: 3 agents handling ticket triage, response drafting, and knowledge base maintenance
- Engineering: 4 agents for CI/CD automation, code review, incident response, and documentation
- Finance: 2 agents for invoice processing and expense categorization
- Marketing: 2 agents for content scheduling and analytics reporting
- Executive: 1 agent for daily briefing preparation
That is 12 agents, each with its own YAML policy file, its own sandbox configuration, its own API credentials, and its own cost profile. Without centralized governance, three problems emerge within the first 90 days:
Day 90 Without Control Plane
Policy drift: The engineering team updated their CI/CD agent’s YAML policy 3 times since initial deployment. The security team reviewed the first version. Nobody reviewed versions 2 and 3. The latest version includes a wildcard host pattern that the engineer added for convenience during a late-night debugging session and never removed.
Inconsistent configurations: The finance and marketing agents were configured by different engineers. The finance agent runs on NemoClaw 0.4.2 with seccomp enabled. The marketing agent runs on NemoClaw 0.3.8 with a known seccomp bypass. Nobody tracks which version each agent runs.
Compliance gaps: The quarterly SOC2 audit asks: “List all AI agents, their permissions, and their data access scope.” The IT team spends 3 days manually SSHing into 12 machines to collect policy files, version numbers, and audit logs. The auditor finds 2 agents with stale credentials and 1 agent with filesystem write access to /home/.
This is the governance gap. NemoClaw provides the security primitives for each individual agent. But NemoClaw does not provide fleet-wide visibility, centralized policy management, or automated compliance reporting. Each agent is a security island — hardened in isolation, ungoverned as a fleet.
NemoClaw Handles Security. JetPatch Handles Operations.
The clearest way to understand the NemoClaw + JetPatch architecture is as two distinct layers, each with a defined responsibility boundary. Mixing the two leads to architectural confusion. NemoClaw is not a governance platform. JetPatch is not a sandbox.
| Responsibility | NemoClaw (Security Layer) | JetPatch (Operations Layer) |
|---|---|---|
| Sandbox isolation | OpenShell kernel sandbox (Landlock, seccomp, namespaces) | Not involved — trusts NemoClaw’s enforcement |
| Policy enforcement | 4-level evaluation engine (binary, destination, method, path) | Not involved — NemoClaw enforces at runtime |
| Data privacy | Privacy router (local vs cloud inference routing) | Not involved — routing decisions are NemoClaw’s |
| Policy distribution | Manual (copy YAML files to each agent) | Centralized push to all agents from single console |
| Lifecycle management | Not provided | Deploy, update, rollback, retire agents fleet-wide |
| Compliance reporting | Audit logs per agent (raw log files) | Aggregated dashboards, SOC2/HIPAA report generation |
| Fleet management | Not provided | Agent inventory, version tracking, health monitoring |
| Cost allocation | Not provided | Per-agent, per-department API cost tracking |
The key architectural point: JetPatch does not replace or modify NemoClaw’s security controls. The sandbox still runs at the kernel level. The policy engine still evaluates every action. The privacy router still makes routing decisions. JetPatch operates above NemoClaw, managing the fleet of NemoClaw-secured agents as governed corporate assets rather than isolated technical deployments.
“NemoClaw secures the agent. JetPatch governs the fleet. These are complementary layers, not competing products.”
— JetPatch Enterprise Control Plane documentation, March 2026
“OpenShell Redraws the Agent Control Plane, Enforces Governance.”
— Futurum Group analysis, March 2026 — positioning the key question: “Open standard or product launch?”
The Futurum Group analysis captures the strategic tension: NemoClaw’s OpenShell could become an open standard for agent security, or it could remain an NVIDIA-specific product. JetPatch’s role is significant either way — as PRNewswire coverage noted, JetPatch “transforms the complex policy.yaml management of OpenShell into a scalable enterprise workflow.” Whether OpenShell becomes a standard or a product, enterprises need the operational layer that JetPatch provides.
JetPatch’s NemoClaw integration is not happening in isolation. GitHub announced “Enterprise AI Controls & agent control plane” as generally available on February 26, 2026 (GitHub Changelog). This signals a broader market movement toward agent governance infrastructure across the industry. Enterprise buyers evaluating NemoClaw + JetPatch should understand that agent control planes are becoming a standard enterprise requirement — not just a NemoClaw-specific concern. The organizations investing in governance infrastructure now are positioning for a market that every major platform vendor is building toward.
What the Enterprise Control Plane Actually Does: 5 Capabilities
1. Centralized Policy Distribution
Without a control plane, updating a YAML policy across 12 agents means SSHing into 12 machines (or pushing through 12 CI/CD pipelines) and verifying each deployment. With JetPatch, a policy update is a single action from a central console. The control plane pushes the updated policy to all targeted agents, verifies each agent received and applied the update, and reports any failures. Version history is maintained centrally — you can see that Agent-07 is running policy v2.3 while all other agents are on v2.4 and investigate why.
2. Agent Lifecycle Management
Agents have lifecycles: they are provisioned, configured, deployed, updated, and eventually retired. Without lifecycle management, retired agents continue running because nobody remembered to shut them down. Orphaned agents consume compute resources, hold active API credentials, and represent an expanding attack surface. JetPatch tracks every agent from provisioning to retirement: deployment date, current version, policy version, last activity timestamp, and current status. An agent that has not reported activity in 30 days gets flagged for review. An agent running an end-of-life NemoClaw version gets flagged for upgrade.
JetPatch’s kill-switch capability goes beyond NemoClaw’s per-agent termination. When triggered from the control plane, the kill switch can instantly pause or suspend autonomous agent processes across global infrastructure (PRNewswire). This is not “send a shutdown request and wait for graceful termination.” This is immediate suspension across every agent in the fleet, or targeted suspension of specific agents by department, role, or policy version. In a security incident — a compromised model, a data exfiltration attempt detected by CrowdStrike Falcon, a rogue agent identified by anomaly detection — the kill switch stops damage propagation in seconds, not minutes. For regulated industries where an uncontrolled agent could trigger a compliance violation measured in millions of dollars, fleet-wide kill-switch capability is not optional.
3. Compliance Reporting
When the SOC2 auditor asks for a list of all AI agents, their permissions, and their last security review date, the control plane generates that report in seconds — not days. Compliance dashboards show which agents have current policy reviews, which agents have audit logging enabled, and which agents are running versions with known security advisories. For organizations subject to HIPAA, the control plane can generate evidence packages showing that all agents processing PHI route inference through local Nemotron models and never call cloud APIs. The EU AI Act requires organizations to maintain documentation of AI system behavior — the control plane’s agent activity history satisfies this requirement automatically.
4. Fleet-Wide Health Monitoring
A single NemoClaw deployment generates audit logs on one machine. Twelve deployments generate audit logs on 12 machines. Without aggregation, correlating agent behavior across the fleet requires manual log collection and analysis. The control plane aggregates health metrics from all agents into a single dashboard: uptime, policy denial rates, error rates, latency, and resource consumption. Anomaly detection flags unusual patterns — an agent that suddenly starts generating 10x its normal volume of API calls, or an agent whose policy denial rate spikes from 2% to 40%.
5. Cost Allocation by Department
Enterprise AI agent deployments consume API costs (LLM inference), compute costs (sandbox hosting), and engineering costs (policy maintenance). The control plane tracks API usage per agent and attributes costs to the department that owns each agent. When the CFO asks why the AI infrastructure bill doubled in Q2, the answer is specific: the engineering department’s code review agent increased its Claude API usage by 300% because the team expanded its scope from pull request summaries to full code analysis. Cost visibility prevents budget surprises and enables informed decisions about agent deployment ROI.
OWASP ASI10 (Rogue Agents): Why Governance Prevents Agent Drift at Scale
OWASP’s Agentic Security Initiative identifies ASI10 — Rogue Agents — as the risk of AI agents operating outside their intended boundaries. At the individual agent level, NemoClaw’s sandbox and policy engine prevent this: an agent physically cannot exceed its YAML-defined permissions. But ASI10 at scale is a governance problem, not just a security problem. An agent can operate within its policy permissions and still behave in ways the organization did not intend — if the policy itself drifted from the approved baseline.
Consider this scenario: An engineer adds files.upload to a Slack agent’s YAML policy because a stakeholder requested file-sharing capability. The engineer tests it. The feature works. The updated policy is deployed. But the security team never reviewed the change, and files.upload allows the agent to exfiltrate data via Slack file attachments. The agent is not rogue in the NemoClaw sense — it is operating within its policy. But it is rogue in the organizational sense — it has capabilities that were never approved through the governance process. See our OWASP Agentic Top 10 analysis for the full ASI framework.
The control plane prevents this by enforcing a policy approval workflow. Policy changes are submitted to the control plane, which routes them through the security team’s review queue before deployment. No agent receives an updated policy without approval. The control plane maintains a complete history of every policy version, who approved it, and when. This is governance as code — the same rigor that enterprises apply to infrastructure-as-code (Terraform, Kubernetes manifests) applied to agent permissions.
Policy drift is the operational equivalent of configuration drift in infrastructure management. Without centralized governance, individual agents accumulate one-off permissions that diverge from the approved baseline. After 6 months, no two agents in the fleet have identical security postures, and the security team has no visibility into which agents have drifted. The control plane detects drift by comparing each agent’s running policy against the approved baseline and flagging discrepancies.
NemoClaw + JetPatch vs Microsoft Agent Governance Toolkit
Microsoft announced the Agent Governance Toolkit in March 2026, targeting general availability in May 2026 at $15/user/month. The toolkit provides OWASP Agentic Top 10 coverage (all 10 categories), agent lifecycle management, policy enforcement, and compliance reporting — tightly integrated with the Microsoft 365 ecosystem and Azure infrastructure. It is the most direct competitor to the NemoClaw + JetPatch stack.
The comparison is not “which is better” but “which architecture fits your organization.”
| Dimension | NemoClaw + JetPatch | Microsoft Agent Governance Toolkit |
|---|---|---|
| OWASP ASI coverage | 10/10 (NemoClaw sandbox + policy engine + JetPatch governance) | 10/10 (built-in coverage across all categories) |
| Sandbox technology | Kernel-level (Landlock, seccomp, namespaces) | Application-level (Azure service boundaries) |
| Pricing model | Open-source NemoClaw + JetPatch licensing | $15/user/month (Microsoft 365 add-on) |
| Infrastructure | Runs on your Linux infrastructure (any cloud or on-prem) | Requires Azure and Microsoft 365 |
| LLM flexibility | Any model (Nemotron, Claude, GPT, Llama, Mistral) | Azure OpenAI Service (primary), limited third-party |
| Data residency | Full control via privacy router (local inference available) | Azure region-bound, Microsoft processes telemetry |
| Vendor lock-in | Open-source NemoClaw, portable YAML policies | Deep Microsoft 365/Azure dependency |
| GA timeline | NemoClaw: alpha (March 6 open-source, March 16 GTC launch). JetPatch: announced March 18, early-access available now. | May 2026 (announced) |
| Best fit | Multi-cloud/on-prem, regulated industries, FOSS preference | Microsoft-first shops, Azure-native infrastructure |
The architectural difference: Microsoft’s approach is application-level governance within their cloud ecosystem. NemoClaw + JetPatch provides kernel-level security with an independent governance layer. For organizations in regulated industries — healthcare, finance, government — where data residency requirements mandate on-premises inference and infrastructure control, the open-source stack provides capabilities that a cloud-only governance tool cannot. For organizations already invested in Microsoft 365 with Azure infrastructure and no on-premises requirements, Microsoft’s integrated approach reduces operational complexity.
NemoClaw is in alpha as of March 2026. NVIDIA has been transparent about this. Microsoft’s Agent Governance Toolkit has a May 2026 GA target but is not shipping yet either. Both products are early. Enterprise decision-makers should evaluate both on architecture fit and vendor alignment, not current feature completeness. The organizations deploying governance infrastructure now — even on alpha platforms — will be 6–12 months ahead of those who wait for GA releases.
JetPatch’s control plane integrates with CrowdStrike Falcon, connecting autonomous agent operations with broader enterprise security workflows (PRNewswire). This means agent anomalies detected by Falcon’s AIDR — unusual API call patterns, unexpected binary executions, lateral movement attempts — can trigger JetPatch governance actions automatically. A Falcon alert about suspicious agent behavior can trigger a JetPatch policy lockdown or kill-switch activation without waiting for a human to SSH into the affected host. For organizations already running Falcon as their EDR platform, this integration closes the gap between agent detection (Falcon) and agent governance response (JetPatch).
Day-to-Day Operations with the Control Plane
What does operating a governed agent fleet look like in practice? Here is the workflow for 3 common enterprise scenarios, showing how the NemoClaw + JetPatch stack handles each one.
Scenario 1: Deploying a New Agent
-
1
Engineer authors YAML policy following the organization’s policy template. The policy defines binaries, network destinations, HTTP methods, paths, and filesystem access. See our Policy Engine Cookbook for production-ready templates.
-
2
Policy submitted to JetPatch control plane for review. The control plane runs automated validation (no wildcards, no root filesystem access, audit logging enabled) and routes to the security team’s approval queue.
-
3
Security team reviews and approves. The control plane records the approver, timestamp, and policy version. This becomes part of the compliance evidence package.
-
4
Control plane deploys the agent to the target infrastructure with the approved policy. NemoClaw provisions the sandbox, applies the YAML policy, and starts the agent. The control plane monitors the deployment and confirms the agent is running in sandboxed mode.
-
5
Agent appears in the fleet dashboard with its policy version, deployment date, owning department, and cost center tag. The compliance dashboard automatically includes the new agent in the next SOC2 report generation.
Scenario 2: Responding to a Security Advisory
NVIDIA publishes a security advisory for NemoClaw 0.4.x with a recommended upgrade to 0.4.3. Without a control plane, the IT team must identify which agents run affected versions (manual SSH, manual version checks) and then upgrade each one individually. With JetPatch, the workflow is:
-
1
Control plane queries fleet: “Show all agents running NemoClaw < 0.4.3.” Response: 4 agents out of 12 are affected.
-
2
IT team initiates fleet-wide upgrade targeting the 4 affected agents. The control plane schedules rolling upgrades during each agent’s maintenance window.
-
3
Control plane monitors each upgrade, verifying the agent starts successfully on the new version and passes health checks. Failed upgrades trigger automatic rollback and alert.
-
4
Compliance dashboard updates to show 12/12 agents on patched versions. The advisory response timeline is recorded for SOC2 evidence.
Scenario 3: Quarterly Compliance Review
The SOC2 auditor requests documentation of all AI agent deployments, their security controls, and evidence of ongoing governance. Without a control plane, this takes days of manual collection. With JetPatch:
-
1
Generate agent inventory report: All 12 agents listed with deployment date, NemoClaw version, policy version, last policy review date, owning department, and current status.
-
2
Generate policy review history: Every policy change, who approved it, and the diff between versions. Evidence that all policy changes went through security review.
-
3
Generate audit log summary: Aggregated policy denials, security events, and anomaly alerts across the fleet for the audit period.
-
4
Export compliance package in auditor-ready format (PDF or structured data). Total time: minutes, not days.
When You Need a Control Plane: The 3-Agent Threshold
Not every NemoClaw deployment needs a governance layer. A single-agent deployment — one agent, one policy, one engineer monitoring it — does not justify the operational overhead of a control plane. The inflection point is somewhere between 3 and 5 agents, depending on your organization’s compliance requirements.
| Agent Count | Governance Approach | Recommended Tools |
|---|---|---|
| 1–2 agents | Manual governance is sufficient. Version-control YAML policies. Security team reviews diffs. | NemoClaw + Git + manual monitoring |
| 3–5 agents | Manual governance becomes fragile. Policy drift risk increases. Consider centralized tooling. | NemoClaw + basic automation scripts |
| 6–15 agents | A control plane pays for itself. Policy distribution, compliance reporting, and fleet visibility save significant operational time. | NemoClaw + JetPatch Enterprise Control Plane |
| 15+ agents | A control plane is a requirement, not an option. Without one, governance is manual, inconsistent, and audit-failing. | NemoClaw + JetPatch + dedicated governance team |
The compliance trigger also matters. If your organization is subject to SOC2, HIPAA, or the EU AI Act (full enforcement August 2026), the documentation and audit trail requirements effectively mandate centralized governance at any agent count above 2. A SOC2 auditor asking about AI agent controls does not accept “we manage them individually via SSH.” They expect systematic governance with evidence.
The Open-Source Stack vs Vendor-Locked Governance
The NemoClaw + JetPatch stack represents an open-source-first approach to agent governance. NemoClaw is open source (NVIDIA), policies are portable YAML files, and the governance layer operates independently from the security layer. If JetPatch were to disappear tomorrow, your NemoClaw agents continue running with their existing policies. You lose fleet management, not agent security.
Contrast this with Microsoft’s Agent Governance Toolkit, which is integrated into the Microsoft 365 ecosystem. If you adopt it, your agents run on Azure, your policies are stored in Microsoft’s infrastructure, and your governance data lives in Microsoft’s compliance center. This is not inherently worse — Microsoft’s integration depth means less operational complexity for Microsoft-native organizations. But it creates vendor dependency. Migrating governance from Microsoft’s toolkit to an alternative requires re-implementing policy management, compliance reporting, and fleet visibility from scratch.
For enterprise architects making this decision, the question is: does your organization value infrastructure portability (choose NemoClaw + JetPatch) or operational simplicity within an existing vendor ecosystem (choose Microsoft)? Both are valid. The wrong answer is choosing neither and managing a growing agent fleet with SSH and spreadsheets.
Frequently Asked Questions
Does JetPatch modify NemoClaw’s security controls?
No. JetPatch operates above NemoClaw’s security layer. It manages policy distribution, lifecycle, and compliance reporting, but it does not intercept, modify, or override NemoClaw’s sandbox enforcement, policy engine decisions, or privacy router routing. If NemoClaw’s policy engine denies an action, JetPatch cannot override that denial. The control plane is an operational tool, not a security tool.
Can we use JetPatch with agents that are not running NemoClaw?
The Enterprise Control Plane announced in March 2026 is specifically designed for NemoClaw deployments. JetPatch’s broader platform supports other agent runtimes, but the NemoClaw-specific features (YAML policy distribution, sandbox health monitoring, privacy router status) require NemoClaw. For mixed-runtime environments, consult JetPatch’s documentation on multi-runtime governance.
What does JetPatch cost?
JetPatch’s Enterprise Control Plane pricing is not publicly listed as of March 2026. Contact JetPatch directly for enterprise pricing. When evaluating TCO, compare the control plane cost against the operational cost of manual governance: the engineering hours spent on manual policy distribution, the compliance team hours spent collecting audit evidence, and the risk cost of policy drift going undetected for months.
How does this integrate with ManageMyClaw’s managed care?
ManageMyClaw’s Enterprise Managed Care ($2,500–$10,000/month) includes NemoClaw stack management, policy updates, and compliance monitoring. For organizations using JetPatch as their control plane, ManageMyClaw operates as the managed service provider within the JetPatch governance framework — handling the day-to-day policy authoring, security reviews, and optimization recommendations that the control plane tracks and reports on. The control plane provides visibility; ManageMyClaw provides the operational expertise.
Is there a timeline for NemoClaw general availability?
NVIDIA has not announced a GA date for NemoClaw as of March 2026. The current release is alpha. Based on the 17 launch partners (Adobe, Salesforce, SAP, CrowdStrike, and others) and the JetPatch control plane announcement, the ecosystem is building toward production readiness. Organizations deploying governance infrastructure now will be positioned to scale when NemoClaw reaches GA. Those who wait for GA before starting governance planning will be 6–12 months behind.
Our $2,500 Assessment reviews your agent fleet architecture, maps governance requirements, and recommends the right control plane strategy for your organization. 1 week. Written report. Executive briefing included.
Schedule Architecture Review