“48% of CISOs now rank agentic AI as their number-one attack vector. NVIDIA responded by wrapping OpenClaw in a security runtime. The question for your organization: does that wrapper cover enough?”
— Dark Reading CISO Survey, 2026
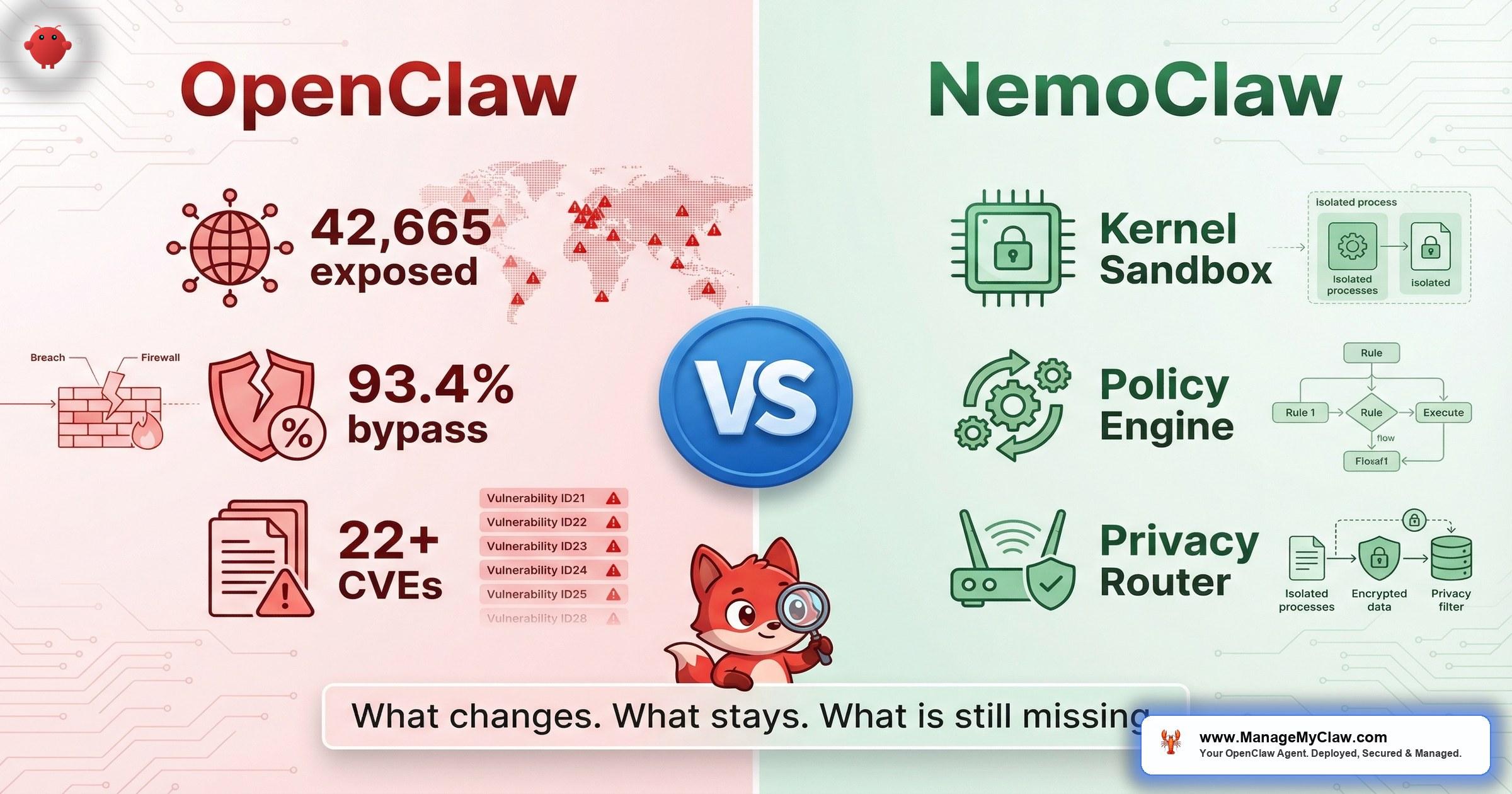
On March 16, 2026, NVIDIA announced NemoClaw at GTC — a security stack that wraps OpenClaw in kernel-level sandboxing, a YAML-configured policy engine, and a privacy router for data sovereignty. 17 launch partners committed: Adobe, Atlassian, Cisco, CrowdStrike, Salesforce, SAP, ServiceNow, Red Hat. TechCrunch headlined it: “Nvidia’s version of OpenClaw could solve its biggest problem: security.”
That headline captures the aspiration. This analysis covers the engineering reality.
NemoClaw is still OpenClaw under the hood, but now in a locked, turbocharged sandbox. For CTOs and CISOs evaluating whether NemoClaw closes the security gap enough for enterprise deployment — or whether staying with vanilla OpenClaw plus defense-in-depth is the pragmatic path — the answer depends on which gaps your organization actually needs closed. This post maps every NemoClaw control to a specific OWASP Agentic Security Index category, identifies what remains unaddressed, and outlines the governance considerations that no security wrapper can solve alone.
Vanilla OpenClaw in Production: The Risk Surface
Before evaluating what NemoClaw adds, your security team needs to understand what vanilla OpenClaw exposes. The data is not theoretical — it is documented, quantified, and ongoing.
Exposed OpenClaw instances (Maor Dayan, security researcher)
Authentication bypass rate across scanned deployments
Security researcher Maor Dayan’s scan of public-facing OpenClaw deployments found 42,665 exposed instances across 52 countries — with the US and China representing the largest concentrations — and a 93.4% authentication bypass rate. Dayan called it “the largest security incident in sovereign AI history.” OpenClaw has accumulated 22+ CVEs since launch, including CVE-2026-25253: a one-click remote code execution vulnerability affecting all versions before 2026.1.29 that left 17,500 internet-exposed instances vulnerable to a single exploit (CSO Online, Conscia). Automated scanners — the tools most security operations centers rely on for vulnerability detection — miss 91% of OpenClaw-specific attack vectors.
“Within three weeks of OpenClaw’s popularity surge: a critical RCE CVE, large-scale supply chain poisoning, and systemic architectural weaknesses. Roughly 20% of all published skills — approximately 900 community-built packages — were confirmed malicious.”
— Maor Dayan (Medium) & Bitdefender via Conscia
Vanilla OpenClaw grants agents filesystem, network, and process access with no kernel-level enforcement boundary. The agent’s own instruction-following is the primary access control mechanism — a control that prompt injection, context compaction, and tool-chain manipulation can all bypass.
The OpenClaw documentation itself states that the platform “assumes one trusted operator boundary per gateway.” In enterprise environments with multiple teams, departments, and compliance domains, that single-operator assumption creates an architectural constraint that no configuration change can fully resolve. Your deployment is either single-tenant by design, or it is operating outside the documented trust model.
CrowdStrike’s 2026 Global Threat Report documented an 89% year-over-year increase in AI-enabled attacks. Average eCrime breakout time fell to 29 minutes. The fastest observed was 27 seconds. When NVIDIA stood on the GTC stage and announced NemoClaw, it was acknowledging what the security community had been documenting for months: the default OpenClaw deployment model does not meet enterprise security requirements.
What NemoClaw Actually Adds to OpenClaw
NemoClaw is a stack, not a product. It combines OpenClaw (unchanged), NVIDIA OpenShell (the new open-source security runtime, Apache 2.0 licensed), and NVIDIA Nemotron models for local inference. The relationship is precise: NemoClaw runs OpenClaw inside it. As Second Talent and Yotta Labs explain, “It’s a security and governance layer that wraps around OpenClaw, a plugin and a runtime that add enterprise-grade controls without modifying the agent code itself.” The New Stack describes the goal: “The idea is for NemoClaw to become something akin to an enterprise-grade distribution of OpenClaw.”
The distinction from container-level isolation is critical. As Katonic AI states: “Docker isolates processes. NemoClaw controls agent BEHAVIOUR inside the container.” NemoClaw adds 4 isolation layers at the kernel level — network, filesystem, process, and inference — and the agent cannot override any of them. The security value comes from 3 controls that OpenShell wraps around OpenClaw at the operating system level.
Control 1: Kernel-Level Sandbox (OpenShell)
OpenShell sandboxes at the process level, controlling filesystem access, process execution, and network behavior through kernel enforcement. This is architecturally different from Docker container isolation, which operates at the namespace and cgroup level. OpenShell adds deny-by-default filesystem policies via Landlock LSM, network namespace rules for egress control, and seccomp filter profiles that restrict which system calls the agent process can invoke.
“OpenShell operates outside the agent, not inside it. Tools like Claude Code and Cursor ship with internal guardrails. But those protections live inside the agent’s own process. A compromised agent can potentially override them. OpenShell wraps the agent at the operating system level.”
— NVIDIA OpenShell Technical Documentation
The practical implication for your security team: with OpenShell, even if an agent is compromised through prompt injection or a malicious skill, the kernel-level boundary prevents escalation to host-system access. The sandbox is not a configuration file the agent can modify. It is an OS-enforced boundary.
OWASP mapping: Addresses ASI01 (Excessive Agency) and ASI06 (Inadequate Sandboxing). Provides the process-level isolation that enterprise sandboxing frameworks require as a baseline control.
Control 2: YAML Policy Engine
The policy engine is YAML-configured and runs out-of-process — meaning the agent cannot modify its own permissions. Every action is evaluated against a 4-level hierarchy before execution:
- Binary level — which executables the agent can invoke
- Destination level — which network endpoints the agent can reach
- Method level — which HTTP methods are permitted per destination
- Path level — which filesystem paths are readable, writable, or denied
Policy updates are applied live at sandbox scope without requiring agent restart. Every allow and deny decision is logged with full audit trail. For organizations subject to SOC 2 or HIPAA audit requirements, this decision log provides the evidence chain that vanilla OpenClaw’s agent-internal logging cannot.
OWASP mapping: Addresses ASI02 (Prompt Injection resilience at the enforcement layer) and ASI09 (Insufficient Logging and Monitoring). The out-of-process architecture means policy enforcement survives prompt injection — a compromised agent cannot modify permissions it does not control.
Control 3: Privacy Router
The privacy router evaluates each inference request and routes it based on data classification policies. Sensitive context — PII, PHI, proprietary data — stays on-premises and is processed by local Nemotron models running on NVIDIA GPU hardware. Specifically, NemoClaw is optimized for Nemotron 3 Super 120B — a hybrid Mamba-Transformer MoE architecture with 120B total parameters but only 12B active at inference time, delivering strong capability at manageable compute cost (glbgpt.com). Non-sensitive requests route to frontier cloud models for maximum capability. PII is stripped or redacted using differential privacy technology before anything reaches an external API. Every routing decision is logged.
Privacy Router
A healthcare organization deploys NemoClaw for clinical documentation assistance. Patient data routes through local Nemotron on the organization’s DGX infrastructure — PHI never leaves the facility network. General medical reasoning — drug interaction lookups, clinical guideline summaries — routes to Claude or GPT-5 for superior capability. The privacy router enforces this split at the infrastructure level, not through agent instructions.
This is the use case where NemoClaw’s privacy architecture provides genuine, differentiated value over any other OpenClaw deployment model.
OWASP mapping: Addresses ASI05 (Insecure Output Handling by preventing sensitive data leakage to external APIs) and supports ASI10 (Inadequate Data Protection). For regulated industries, this is the control that maps most directly to HIPAA, GDPR, and EU AI Act data residency requirements.
OpenClaw vs. NemoClaw: Control-by-Control
| Security Control | Vanilla OpenClaw | NemoClaw (OpenShell) |
|---|---|---|
| Process isolation | Docker namespaces (if manually configured) | Kernel-level sandbox with Landlock + seccomp |
| Filesystem access | Full host access unless Docker volume mounts restricted | Deny-by-default; Landlock LSM enforcement |
| Network egress | Unrestricted unless DOCKER-USER iptables rules configured | Network namespace rules; policy-enforced egress |
| Policy enforcement | AGENTS.md (agent-internal, bypassable) | Out-of-process YAML engine (agent-external) |
| Policy granularity | Tool-level allowlists | 4-level: binary, destination, method, path |
| Audit trail | Agent logs (if configured; no tamper protection) | Full allow/deny decision log (out-of-process) |
| Data privacy routing | All data goes to 1 model provider | Privacy router with PII stripping and local/cloud split |
| Local inference | Possible but not guided | Nemotron models pre-configured for on-premises use |
| Multi-tenancy | “One trusted operator boundary per gateway” | Not multi-tenant (same single-operator model) |
The table makes the pattern clear. NemoClaw significantly improves 3 layers: process isolation, policy enforcement, and data privacy. It does not change the underlying OpenClaw architecture, the trust model, or the operational complexity of running AI agents in production.
What NemoClaw Cannot Fix
This is the section your CISO needs to read before approving a deployment. NemoClaw addresses real gaps. It also leaves real gaps unaddressed — some of them architectural, some of them documented in peer-reviewed security research. Honest evaluation requires both columns.
- No published performance benchmarks — NVIDIA has not released latency, throughput, or resource overhead data for OpenShell’s sandbox or privacy router in production workloads. Your capacity planning has no vendor-supplied baseline.
- Full privacy router requires NVIDIA hardware — Local Nemotron inference requires GPU infrastructure (GeForce RTX, RTX PRO, or DGX systems). Organizations running OpenClaw on cloud VPS infrastructure cannot use the privacy router’s local routing capability without provisioning GPU compute.
- Not multi-tenant — NemoClaw inherits OpenClaw’s single-operator trust boundary. Departments sharing a NemoClaw gateway do not get tenant-level isolation, per-department policy enforcement, or cost allocation. Enterprise governance requires multi-tenancy that the architecture does not support.
- No independent security audit — As of March 2026, no third-party penetration test or security audit of OpenShell has been published. The 17 launch partners are integration partners, not security auditors. The community is already testing boundaries — one r/LocalLLaMA post documented bypassing NemoClaw’s sandbox isolation entirely.
- Alpha-stage maturity — NVIDIA describes NemoClaw as early-access/alpha. Production stability, backward compatibility, and upgrade path guarantees are not available. Enterprise procurement teams evaluating vendor risk should factor this maturity level into their assessment.
Verified Sandbox and Policy Bypasses
Independent security researchers have documented specific architectural vulnerabilities that NemoClaw’s wrapper cannot fix because they exist in the underlying OpenClaw platform. These are not theoretical — they are published, reproducible, and unpatched.
Critical
Snyk Labs published “Escaping the Agent: On Ways to Bypass OpenClaw’s Security Sandbox” documenting a direct sandbox escape via the /tools/invoke endpoint. Even with workspaceAccess set to “none” or “ro”, a sandboxed model can exfiltrate or overwrite arbitrary host files. The vulnerability exists at the API level — NemoClaw’s kernel-level sandbox operates on process boundaries, but the /tools/invoke endpoint executes within the trusted process context.
This means a compromised agent can read and write files outside the sandbox boundary through a legitimate API call that the policy engine does not intercept.
High
The same Snyk Labs research identified a Time-of-Check to Time-of-Use (TOCTOU) race condition in sandbox path validation. The sandbox validates a file path at check time, but by the time the operation executes, the path can be swapped — allowing a sandboxed session to escape the workspace boundary and access the host filesystem. This is a class of vulnerability that kernel-level sandboxing does not inherently prevent because the race exists between the validation and execution layers.
Network policy presets are missing a binary restriction. Any process running within a sandbox that has allowed network endpoints can reach those endpoints — regardless of which binary initiates the connection. The 4-level policy hierarchy (binary, destination, method, path) has an enforcement gap: the binary restriction does not apply to network presets. This means an agent that spawns a subprocess inherits network access that the policy was intended to restrict.
Penligent.ai documented a prompt injection path that bypasses both tool control and audit logging. If an agent executes unintended code via prompt injection, that code can use curl or python3 to POST data to any endpoint the network preset allows. The exfiltration happens through legitimate system binaries, not through the tool framework — so NemoClaw’s tool-level audit trail records no anomaly. The data leaves through a channel the policy engine considers authorized.
No path currently exists in OpenShell 0.0.10 to route inference to a local Ollama instance running on WSL2. Enterprise teams deploying on Windows Server infrastructure with WSL2 cannot use the local inference capability that the privacy router depends on. Local options are described as experimental. This limits the privacy router’s data-sovereignty value to Linux-native deployments with direct NVIDIA GPU access.
Independent third-party security audits of OpenShell published as of March 2026
The Penligent.ai analysis summarized it precisely: NemoClaw changes what the security wrapper can enforce, but it still cannot fix the underlying OpenClaw vulnerabilities, the single-operator trust model, or the absence of enterprise governance primitives like role-based access control, department-level cost allocation, and multi-agent orchestration policies. The Snyk Labs findings add a harder edge to that assessment: even the enforcement boundary itself has documented escape paths through /tools/invoke and TOCTOU race conditions that operate below the policy engine’s visibility.
For organizations evaluating NemoClaw against OWASP Agentic Top 10 requirements, the coverage map looks like this:
| OWASP ASI Category | NemoClaw Coverage | Remaining Gap |
|---|---|---|
| ASI01 — Excessive Agency | Kernel sandbox limits process capabilities | Agent still has full capability within sandbox boundaries |
| ASI02 — Prompt Injection | Policy engine survives injection (out-of-process) | Agent logic itself remains vulnerable to manipulation |
| ASI05 — Insecure Output | Privacy router strips PII before external routing | Classification accuracy depends on Nemotron model quality |
| ASI06 — Inadequate Sandboxing | Strong improvement over Docker-only isolation | Snyk Labs documented /tools/invoke bypass and TOCTOU race condition; sandbox escape paths exist |
| ASI09 — Insufficient Logging | Full decision audit trail | No SIEM integration out of box; requires custom pipeline |
| ASI10 — Data Protection | Local routing for sensitive data | Requires GPU hardware; cloud-only deployments excluded |
| ASI03-04, ASI07-08 | Not addressed | Tool poisoning, supply chain, identity, credential management remain open |
What Independent Engineers Are Finding
Enterprise security decisions should not rely on vendor announcements alone. Independent technical evaluation from the engineering community provides signal that vendor documentation does not.
Within days of the GTC announcement, independent engineers published findings that CISOs should factor into their evaluation. A technical analysis on Penligent.ai dissected NemoClaw’s architecture and concluded that while the 3 security controls represent genuine improvements, NemoClaw “still cannot fix” several categories of OpenClaw vulnerability — including the 22+ CVEs in the base platform and the single-operator trust boundary.
An independent engineer documented a method for bypassing NemoClaw’s sandbox isolation to run a fully local agent outside OpenShell’s enforcement boundary. Snyk Labs subsequently published formal research — “Escaping the Agent: On Ways to Bypass OpenClaw’s Security Sandbox” — confirming that sandbox escape paths exist through the /tools/invoke endpoint and a TOCTOU race condition in path validation, even with workspaceAccess set to "none" or "ro". These are not configuration issues. They are architectural gaps. Until these are patched, enterprise security teams should treat the sandbox as defense-in-depth, not as a trust boundary.
Separate independent analysis fact-checked Jensen Huang’s GTC 2026 OpenClaw claims, testing whether NemoClaw’s stated capabilities match measured behavior. The engineering community’s posture is appropriately skeptical: NemoClaw is evaluated on what it does, not what it promises.
One widely-shared technical assessment stated it directly: “Stop trusting client side sandboxes. NemoClaw does not solve the agent execution problem.” That assessment overstates the case — NemoClaw’s sandbox is kernel-level, not client-side — but the underlying concern is valid. A sandbox is one layer. Enterprise AI agent governance requires multiple layers operating independently.
NanoClaw: The Emerging Third Option
Enterprise evaluations are no longer binary. DEV Community published “Architecting the Agentic Future: OpenClaw vs. NanoClaw vs. Nvidia’s NemoClaw” — a three-way comparison that signals a maturing competitive landscape. NanoClaw is emerging as a lightweight alternative that targets a different deployment profile: teams that need agent orchestration without NVIDIA’s hardware requirements or OpenClaw’s full-stack complexity. Multiple comparison articles have appeared across Second Talent, GLBgpt, AICC, Frank’s World, ShareUHack, and Yotta Labs.
The enterprise positioning is straightforward. As ShareUHack summarizes: “Personal use: OpenClaw is fine with basic hardening. Production, customer data, regulated: NemoClaw is the clear choice.” NanoClaw occupies the space between — teams that have outgrown vanilla OpenClaw but do not have the GPU infrastructure or enterprise governance requirements that make NemoClaw’s full stack necessary. The emergence of NemoClaw.run as a managed hosting platform and DigitalOcean’s one-click NemoClaw droplet tutorial suggest the ecosystem is stratifying into self-hosted, managed, and lightweight tiers.
When NemoClaw Is the Right Choice (And When It Is Not)
The evaluation is not binary. NemoClaw is not “good” or “bad” — it is appropriate or inappropriate depending on your organization’s infrastructure, compliance requirements, and deployment timeline.
NemoClaw Is a Strong Fit When:
- Your organization has NVIDIA GPU infrastructure (DGX, RTX PRO workstations) already deployed or budgeted
- Data sovereignty is a hard compliance requirement — HIPAA, GDPR, EU AI Act data residency rules apply to your AI workloads
- Your security team can write and maintain YAML policy files and integrate the audit trail into your existing SIEM
- Your deployment timeline accommodates alpha-stage software and you have engineering capacity to track OpenShell releases
- You need kernel-level isolation as a defense-in-depth layer on top of your existing container hardening
NemoClaw Is Not Sufficient When:
- Your organization requires multi-tenant isolation between departments or business units
- Your deployment runs on cloud VPS infrastructure without GPU compute
- Your compliance framework requires an independently audited security stack
- Your deployment timeline is measured in weeks, not quarters
- You need credential management, workflow configuration, SIEM integration, and ongoing governance — not just isolation
NemoClaw and managed enterprise governance are not mutually exclusive. The strongest enterprise deployment posture uses NemoClaw’s OpenShell as the kernel-level isolation layer while adding enterprise governance, compliance documentation, credential management, SIEM integration, and multi-agent policy management on top. The question is not whether to use NemoClaw — it is whether NemoClaw alone constitutes sufficient governance for your risk profile.
The 6 Enterprise Requirements NemoClaw Does Not Address
Security isolation is necessary but not sufficient for enterprise AI agent deployment. The following governance requirements exist independent of which sandbox technology your organization selects.
| Requirement | Why It Matters | NemoClaw Status |
|---|---|---|
| Multi-tenant isolation | Departments need separate policy domains, audit trails, and cost allocation | Not supported — single-operator model |
| Credential lifecycle management | OAuth tokens, API keys, and service accounts need rotation, revocation, and audit | Not included |
| Compliance documentation | SOC 2 evidence packages, HIPAA BAA mapping, EU AI Act alignment require documented controls | Audit log exists; compliance mapping does not |
| SIEM/SOC integration | Security operations teams need NemoClaw events in their existing monitoring infrastructure | CrowdStrike Falcon AIDR partnership announced; other SIEM integrations require custom work |
| Ongoing CVE remediation | OpenClaw’s 22+ CVEs require patching within defined SLA windows | NemoClaw wraps OpenClaw but does not patch it; base platform vulnerabilities persist |
| Multi-agent governance | Enterprises deploying 5-50+ agents need orchestration policies, resource allocation, and cross-agent audit | Per-sandbox policies only; no cross-agent governance layer |
JetPatch announced an Enterprise Control Plane for NemoClaw at GTC, signaling that NVIDIA’s partner ecosystem recognizes these governance gaps. CrowdStrike’s Secure-by-Design Blueprint provides a reference architecture for integrating OpenShell with Falcon AIDR. These are early ecosystem signals, not production-ready solutions. Enterprise organizations deploying NemoClaw today will need to build or source these governance layers independently.
The Bottom Line for Enterprise Deployment
NemoClaw represents the most significant security improvement the OpenClaw ecosystem has received since launch. The kernel-level sandbox, out-of-process policy engine, and privacy router address 3 of the highest-severity gaps in vanilla OpenClaw’s security posture. NVIDIA’s commitment of 17 enterprise launch partners and the CrowdStrike integration blueprint provide vendor-ecosystem credibility that no individual security tool could build alone.
The honest assessment: NemoClaw is a strong isolation and data-sovereignty layer. It is not an enterprise governance platform. The distinction matters because enterprise deployment approval requires both — and the gaps between what NemoClaw provides and what your security team, compliance officer, and procurement process require are where deployment risk concentrates.
OWASP Agentic Security Index categories where NemoClaw provides strong coverage
Organizations with NVIDIA GPU infrastructure, internal DevOps capacity, and deployment timelines that accommodate alpha-stage software should evaluate NemoClaw as the isolation layer in a broader governance stack. ManageMyClaw Enterprise provides the governance, compliance documentation, and operational layers that sit above and around NemoClaw’s security runtime — including OpenShell sandbox configuration, YAML policy engine setup, privacy router deployment, CrowdStrike Falcon integration, and ongoing compliance management.
Early adopters who build governance now will be production-ready when NemoClaw reaches general availability. Organizations that wait will be 6-12 months behind their competitors who invested in the governance foundation during the alpha window.
Frequently Asked Questions
Is NemoClaw production-ready for enterprise deployment?
No. NVIDIA classifies NemoClaw as alpha/early-access as of March 2026. The core security primitives — OpenShell sandbox, policy engine, privacy router — function today, and 17 enterprise partners including Adobe, Salesforce, and CrowdStrike have committed to the platform. However, no independent security audit has been published, performance benchmarks are unavailable, and backward compatibility guarantees do not exist. Enterprise organizations deploying now should treat NemoClaw as a defense-in-depth layer within a broader governance framework, not as a standalone security solution.
Does NemoClaw support multi-tenant enterprise deployments?
No. NemoClaw inherits OpenClaw’s architectural assumption of “one trusted operator boundary per gateway.” Departments sharing a NemoClaw deployment do not get tenant-level policy isolation, separate audit trails, or per-department cost allocation. Enterprise organizations requiring multi-tenant governance need to either deploy separate NemoClaw instances per department or layer a governance platform on top.
Can we deploy NemoClaw on our existing cloud infrastructure without NVIDIA GPUs?
Partially. The OpenShell sandbox and policy engine can run on standard Linux infrastructure. However, the privacy router’s local inference capability — which routes sensitive data through on-premises Nemotron models — requires NVIDIA GPU hardware. Without GPU infrastructure, all inference requests route to cloud model providers, and the data-sovereignty benefit of the privacy router is lost. Cloud GPU instances (AWS G-series, GCP T4) are an option but cost 10-20x more than standard compute.
How does NemoClaw map to OWASP Agentic Top 10 (ASI01-ASI10)?
NemoClaw provides strong coverage for 3 ASI categories: ASI01 (Excessive Agency via kernel sandbox), ASI06 (Inadequate Sandboxing via OpenShell), and ASI09 (Insufficient Logging via out-of-process audit trail). It provides partial coverage for ASI02 (Prompt Injection — policy engine survives injection but agent logic remains vulnerable), ASI05 (Insecure Output — privacy router strips PII), and ASI10 (Data Protection — local inference for sensitive data). ASI03, ASI04, ASI07, and ASI08 are not addressed. A complete OWASP Agentic Top 10 compliance posture requires additional controls beyond NemoClaw.
What is the total cost of a NemoClaw enterprise deployment?
NemoClaw itself is free and open-source (Apache 2.0). Infrastructure costs include NVIDIA GPU hardware (DGX Spark starts at approximately $4,757 for the Dell Pro Max GB10; DGX Station systems are significantly higher), Linux compute for the OpenShell runtime, and engineering time for YAML policy configuration, privacy router table setup, SIEM integration, and compliance documentation. Independent NemoClaw consultants charge approximately $150/hour. Production hardening typically requires 2-6 weeks of specialist work depending on deployment complexity.
What are the Snyk Labs sandbox bypass vulnerabilities, and does NemoClaw fix them?
Snyk Labs published research titled “Escaping the Agent: On Ways to Bypass OpenClaw’s Security Sandbox” documenting two critical findings. First, the /tools/invoke endpoint allows a sandboxed model to read and write arbitrary host files even when workspaceAccess is set to “none” or “ro.” Second, a TOCTOU (Time-of-Check to Time-of-Use) race condition in sandbox path validation allows sandboxed sessions to escape workspace boundaries. NemoClaw’s kernel-level sandbox does not fix these because the vulnerabilities operate through legitimate API endpoints and timing gaps within the trusted process context. Enterprise deployments should layer additional file-integrity monitoring and API gateway controls until upstream patches are available.
How does NanoClaw compare to NemoClaw and OpenClaw?
NanoClaw is an emerging lightweight alternative that targets teams who have outgrown vanilla OpenClaw but do not have NVIDIA GPU infrastructure or the enterprise governance requirements that justify NemoClaw’s full stack. DEV Community’s three-way comparison (“Architecting the Agentic Future: OpenClaw vs. NanoClaw vs. Nvidia’s NemoClaw”) positions NanoClaw for mid-tier deployments. For regulated environments with customer data, NemoClaw remains the stronger choice. For personal or small-team use, OpenClaw with basic hardening is sufficient. NanoClaw fills the gap between those two tiers.
Should we wait for NemoClaw GA before deploying AI agents?
That depends on your competitive timeline. Gartner projects 40% of enterprise applications will include AI agents by end of 2026. EU AI Act reaches full enforcement in August 2026. Organizations that build governance frameworks now — using NemoClaw’s alpha as the isolation layer plus enterprise governance for compliance, credential management, and multi-agent policy — will be production-ready when GA ships. Organizations that wait for GA before starting governance work will face a 6-12 month gap versus competitors who invested during the alpha window.
Our NemoClaw Assessment maps your current architecture against OWASP ASI01-ASI10, evaluates OpenShell configuration, and delivers a prioritized remediation plan with executive briefing.
Schedule Architecture Review