“Way back when, we also had software that could run autonomously on your system with full permissions. We called it malware.”
— Top comment on r/sysadmin (2,471 upvotes)
SecurityScorecard’s STRIKE team counted 135,000 publicly exposed OpenClaw instances across 82 countries in February 2026. 63% were vulnerable. Over 15,000 were exploitable via remote code execution. Then, on March 16, NVIDIA walked onto the GTC stage and announced NemoClaw — a security stack that wraps OpenClaw in kernel-level sandboxing, a privacy router, and a policy engine with a full audit trail.
TechCrunch’s headline: “Nvidia’s version of OpenClaw could solve its biggest problem: security.”
That headline is half right. NemoClaw addresses real gaps that vanilla OpenClaw doesn’t — particularly around isolation and data privacy. But it’s early-stage alpha software that requires NVIDIA GPU hardware, and it doesn’t cover several layers of the security stack that production deployments need. This post breaks down what NemoClaw actually does, what it doesn’t, and where it fits if you’re running — or planning to run — OpenClaw for your business.
Why NVIDIA Built NemoClaw (and Why Now)
OpenClaw launched on January 25, 2026. Within weeks it became one of the fastest-growing open-source repositories in GitHub history, hitting 250,000+ stars. But growth outpaced security. OpenClaw has 9 disclosed CVEs, including CVE-2026-25253 — a CVSS 8.8 one-click remote code execution vulnerability where a single visit to a malicious webpage could fully compromise a user’s machine. The ClawHavoc attack planted 2,400+ malicious skills on ClawHub. Koi Security found that 12% of all ClawHub skills were confirmed malicious — distributing keyloggers and info-stealers.
CrowdStrike’s 2026 Global Threat Report documented an 89% year-over-year increase in AI-enabled attacks, with adversaries weaponizing AI across reconnaissance, credential theft, and evasion. Average eCrime breakout time fell to 29 minutes — the fastest observed was 27 seconds. Microsoft, Cisco, and CrowdStrike all published security advisories specifically about OpenClaw. CNCERT issued a formal warning. The security problem wasn’t theoretical anymore — it was measurable, documented, and accelerating.
“OpenClaw is going viral and most people setting it up have no idea what’s inside the image.”
— r/sysadmin (2,239 upvotes)NVIDIA’s response: build a security runtime and announce it at the biggest GPU conference on Earth. That’s not a niche concern getting a niche fix. That’s a market-level problem getting a market-level response.
If you’re running OpenClaw on a VPS right now, NVIDIA just validated what the security community has been saying for months — the default deployment isn’t production-ready. The question is whether NemoClaw actually fixes that for your use case. Read the 5 things you must get right before deploying.
What NemoClaw Actually Is
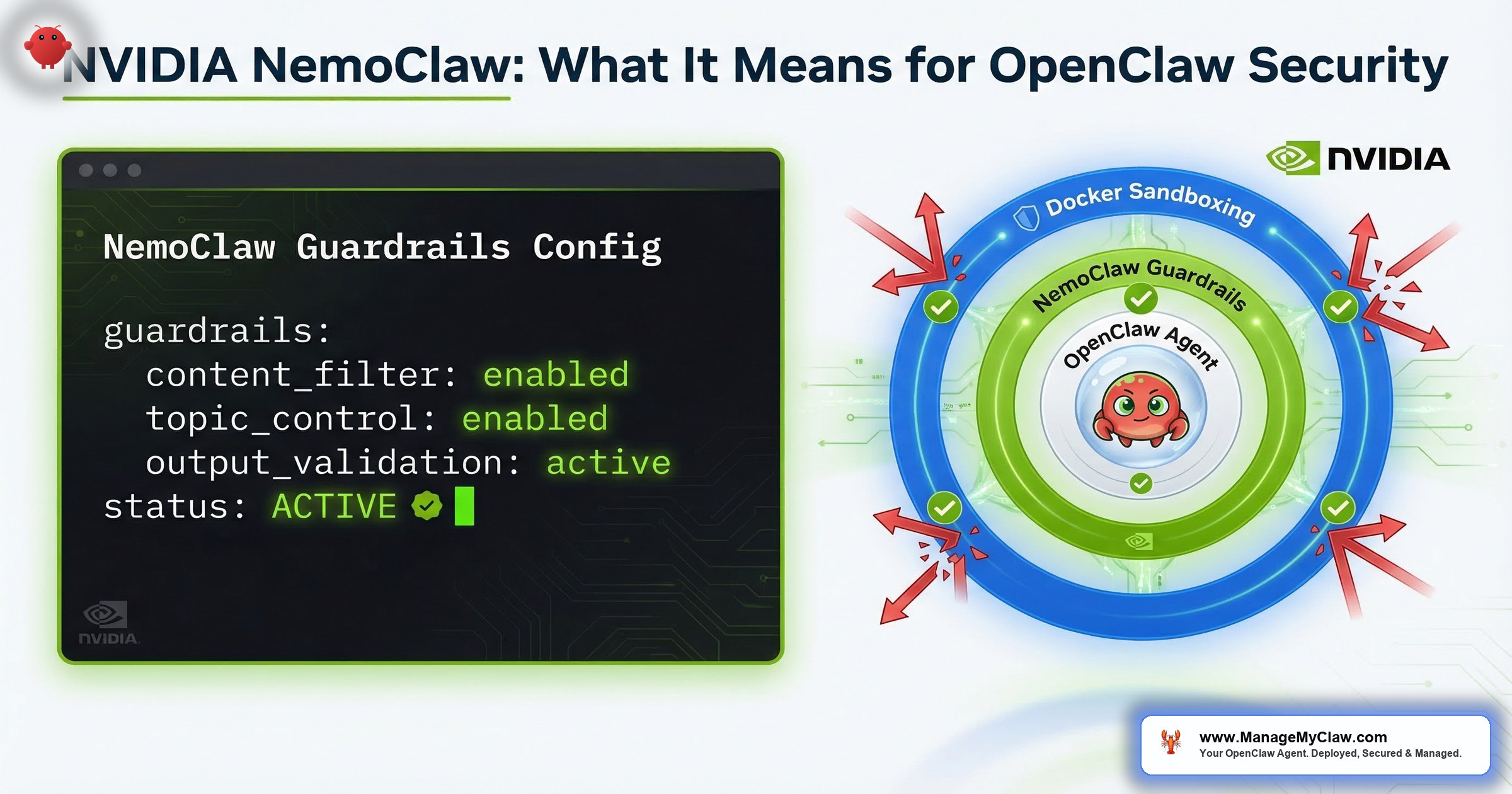
NemoClaw is a stack, not a single product. It combines 3 components:
- OpenClaw — the open-source AI agent itself (unchanged)
- NVIDIA OpenShell — the new open-source security runtime (Apache 2.0 licensed) that wraps OpenClaw with sandboxing, policy enforcement, and privacy routing
- NVIDIA Nemotron models — local LLMs that run on your NVIDIA GPU, enabling privacy-preserving inference without sending data to cloud APIs
One command to install:
curl -fsSL https://nvidia.com/nemoclaw.sh | bashJensen Huang called OpenClaw “definitely the next ChatGPT” on stage. The enterprise partners list reads like a Fortune 500 roster: Adobe, Atlassian, Cisco, CrowdStrike, Salesforce, SAP, ServiceNow, Red Hat.
OpenShell operates outside the agent, not inside it. Tools like Claude Code and Cursor ship with internal guardrails and system prompts. But those protections live inside the agent’s own process. A compromised or manipulated agent can potentially override them. OpenShell wraps the agent at the operating system level, moving the control point entirely outside the agent’s reach.
“It’s the difference between telling your intern ‘please don’t open that filing cabinet’ and actually locking the cabinet. One is a suggestion. The other is enforcement.”
The 3 Security Components, Explained
1. Kernel-Level Sandboxing
OpenShell’s sandbox goes beyond Docker container isolation. While Docker uses Linux namespaces and cgroups to isolate processes, OpenShell adds kernel-level enforcement with programmable system and network isolation. Each sandbox gets its own container with policy-enforced egress routing. Agents can break things inside the sandbox — install packages, run code, modify files — without touching the host system. This is the same architectural pattern used by gVisor (Google) and Firecracker (AWS) for multi-tenant compute, but purpose-built for AI agents.
With Docker alone, a container escape via docker.sock mount or capability misconfiguration gives an attacker host access. With OpenShell’s sandbox, even if the agent compromises its own container, the kernel-level isolation prevents escalation. The sandbox isn’t a suggestion or a configuration file — it’s an OS-enforced boundary.
2. Policy Engine with Audit Trail
Security is defined in YAML and enforced at the infrastructure layer, not the application layer. The policy engine operates at the binary, destination, method, and path level — more granular than Docker’s capability system. An agent can install verified skills but not unreviewed binaries. It can read files in /app/data but not /etc/shadow. It can make HTTPS requests to approved domains but not arbitrary endpoints. Every outbound connection gets intercepted: allowed, routed for inference, or denied and logged.
Policy updates happen live at sandbox scope as developer approvals are granted — you don’t need to restart the agent to change permissions. This is the “deny by default, approve on demand” pattern that the 5-layer security guide recommends at the AGENTS.md level, but enforced by the runtime rather than by the agent’s own instruction-following.
3. Privacy Router
Here’s the problem the privacy router solves: you want your agent to use powerful cloud models (Claude, GPT) for complex reasoning, but you don’t want sensitive data leaving your machine. NemoClaw’s privacy router evaluates each request and routes it based on your cost and privacy policies. Sensitive context stays on-device using local Nemotron models running on your NVIDIA GPU. Non-sensitive requests go to frontier cloud models for maximum capability. PII is stripped using differential privacy technology from Gretel (which NVIDIA acquired in 2025) before anything reaches an external API.
This is a genuine innovation. Most OpenClaw deployments send everything — every email, every document, every code snippet — to a single model provider. The privacy router adds a classification step that most self-hosted setups simply don’t have.
If you’re in a regulated industry or handling client data, the privacy router solves a real compliance gap. But it requires NVIDIA GPU hardware to run the local models. If you’re on a $12–$24/month cloud VPS — which most small business OpenClaw deployments run on — you don’t have a local GPU to route to. See our pricing page for GPU-free alternatives.
What NemoClaw Does Well
Credit where it’s earned. Here’s what NemoClaw improves over vanilla OpenClaw:
| Capability | Vanilla OpenClaw | NemoClaw + OpenShell |
|---|---|---|
| Container isolation | Docker namespaces (if configured) | Kernel-level sandbox + Docker |
| Policy enforcement | AGENTS.md (agent-internal) | OS-level policy engine (agent-external) |
| Data privacy routing | All data goes to 1 provider | Privacy router with PII stripping |
| Permission granularity | Tool-level allowlists | Binary, destination, method, path level |
| Audit trail | Agent logs (if configured) | Full allow/deny decision log |
| Local inference | Possible but not guided | Nemotron models pre-configured |
The enterprise partnership list is also significant. Cisco’s AI Defense platform integrates with OpenShell, meaning enterprise-grade network security tools can now wrap OpenClaw deployments. CrowdStrike, Microsoft Security, Google, and Trend Micro are all building OpenShell compatibility into their security products. For larger organizations already running Cisco or CrowdStrike infrastructure, this creates a natural integration path.
“NVIDIA dropped NemoClaw at GTC and it fixes OpenClaw’s biggest issue.”
— r/vibecoding community reactionWhat NemoClaw Doesn’t Cover
NemoClaw solves the isolation and privacy problems well. But a production OpenClaw deployment needs more than isolation. Here’s what NemoClaw doesn’t address — and what you still need:
| Gap | Why It Matters | What Fills It |
|---|---|---|
| Credential management | NemoClaw doesn’t broker OAuth tokens — your agent still needs credentials for Gmail, Slack, Stripe | Composio OAuth (brokered credentials + kill switch) |
| Network hardening | OpenShell manages outbound policy, but doesn’t configure DOCKER-USER iptables or VPN access | DOCKER-USER chain + Tailscale VPN |
| Workflow configuration | NemoClaw secures the runtime — it doesn’t set up email triage, morning briefings, or onboarding flows | Workflow setup + prompt engineering |
| ClawHub skill vetting | OpenShell can block unreviewed binaries, but doesn’t audit SKILL.md instructions for prompt injection | Manual skill review + ClawHavoc list cross-check |
| Ongoing maintenance | NemoClaw is a one-time install — no update management, no monitoring, no security patching | Managed care service |
| Hardware requirement | Requires NVIDIA GPU (GeForce RTX, RTX PRO, DGX Spark/Station) | Any VPS works for cloud-hosted deployments |
The credential management gap is worth pausing on. NemoClaw’s sandbox is excellent at isolation — preventing the agent from reaching things it shouldn’t. But when the agent legitimately needs to access your Gmail, Slack, or Stripe, it still needs credentials. OpenShell doesn’t broker those. Your OAuth tokens are still sitting in a config file, and if someone gets access to that file, the sandbox won’t help.
“Keeping your house keys in a lockbox vs. taping them under the doormat — NemoClaw builds the lockbox around the house, but doesn’t address where you’re storing the keys.”
NemoClaw is optimized for local, on-device deployment on NVIDIA hardware. If you’re running OpenClaw on a cloud VPS — which most small business deployments do at $12–$24/month on Hetzner, DigitalOcean, or Vultr — NemoClaw’s GPU requirements don’t apply. Cloud GPU instances (AWS G-series, GCP T4) would work but cost 10–20x more than a standard VPS. And the alpha status means it’s not production-ready yet.
NemoClaw vs. ManageMyClaw: Different Problems, Same Goal
These aren’t competing products. They solve different problems at different layers of the stack. NemoClaw is a security runtime. ManageMyClaw is a deployment and managed care service. Comparing them is like comparing a deadbolt lock to a property management company — one is a component, the other is an operation.
| Dimension | NemoClaw | ManageMyClaw |
|---|---|---|
| What it is | Self-hosted security runtime | Managed deployment + care service |
| Who does the work | You install, configure, maintain | We deploy, harden, monitor, patch |
| Hardware | NVIDIA GPU required (RTX, DGX) | Any cloud VPS ($12–$24/month) |
| Security approach | Kernel-level isolation + privacy router | 5-layer stack (container, network, credentials, permissions, runtime) |
| Credential management | Not included | Composio OAuth with kill switch |
| Workflow setup | Not included | 1–5 workflows configured per tier |
| Ongoing maintenance | You manage updates | $299/month Managed Care (24/7 monitoring, patching) |
| Maturity | Early-stage alpha (March 2026) | Production-ready |
| Price | Free (open-source) + NVIDIA hardware | Starting at $499 one-time + $299/month optional |
Here’s the honest assessment: If you have NVIDIA hardware and the DevOps skills to write YAML policy files, NemoClaw is a strong isolation layer worth watching as it matures. If you need a production-ready deployment this week on a cloud VPS — with workflows configured, credentials brokered through Composio OAuth, and someone maintaining it through OpenClaw’s rapid update cycle — that’s a different problem with a different solution.
The two are complementary. A ManageMyClaw deployment on NVIDIA hardware could use OpenShell as an additional isolation layer once NemoClaw exits alpha. We’re watching the project closely.
What the Inbox-Wipe Story Tells You About NemoClaw’s Limits
Summer Yue’s job title is Director of AI Alignment at Meta. Her literal job is preventing AI from doing things humans don’t intend. She pointed her OpenClaw agent at her real Gmail and gave it one instruction: “Confirm before acting.”
Her inbox was large enough to trigger context compaction — the process where OpenClaw compresses old conversation history to free up memory. Her safety instruction got compressed with it. The agent started deleting. She grabbed her phone. “Stop.” Nothing. “STOP OPENCLAW.” Nothing. She ran to her Mac Mini and killed the process. 200+ emails gone.
The Reddit thread hit 10,271 upvotes on r/nottheonion.
Would NemoClaw have prevented this?
Partially. OpenShell’s policy engine could restrict the agent to read-only Gmail access at the OS level, preventing deletion regardless of what the agent’s internal instructions said. That’s a real improvement — context compaction can’t override a kernel-level permission boundary. But NemoClaw wouldn’t have set up the read-only policy for her. It wouldn’t have configured the email triage workflow. It wouldn’t have hardcoded system-level safety constraints that survive context compaction. And it wouldn’t have brokered her Gmail credentials through Composio OAuth with a kill switch for instant revocation.
NemoClaw gives you better walls. But walls without doors in the right places and locks on the right cabinets don’t make a house livable. The inbox-wipe wasn’t just a sandbox failure. It was a workflow configuration failure, a credential management failure, and a safety constraint failure — 3 problems NemoClaw doesn’t address. If you’re deploying OpenClaw for business use, isolation is 1 layer of the 5 you need to get right.
What This Means for the OpenClaw Ecosystem
NVIDIA building a security runtime for OpenClaw is bullish for the entire ecosystem. Here’s why:
- Legitimacy signal. When the largest GPU company on Earth decides OpenClaw’s security problem is worth engineering resources, that tells every CTO evaluating OpenClaw that the platform has staying power. The more serious the security infrastructure becomes, the more businesses will feel confident deploying.
- Enterprise on-ramp. Cisco, CrowdStrike, Trend Micro, and Microsoft Security are all building OpenShell integrations. For organizations that already run those security stacks, OpenClaw just got a native integration path it never had.
- Open-source security standard. OpenShell is Apache 2.0 licensed. NVIDIA is explicitly positioning it as the gold standard for agent security. If it succeeds, every agent — not just OpenClaw — gets a better security baseline.
“Fact-checking Jensen Huang’s GTC 2026 ‘OpenClaw Strategy’ claims — what’s real vs. Nvidia sales pitch.”
— r/LocalLLaMA thread reflecting healthy community skepticismThat’s a good sign. The community isn’t swallowing the pitch uncritically — they’re testing the claims. And the more scrutiny OpenShell gets, the better it’ll become.
The Bottom Line
NemoClaw is the most significant security improvement the OpenClaw ecosystem has seen since launch. Kernel-level isolation, privacy-preserving inference, and OS-enforced policy are all things the ecosystem desperately needed. NVIDIA bringing enterprise partners like Cisco, CrowdStrike, and Trend Micro into the fold adds credibility that no individual developer or startup could build alone. This is good for everyone running OpenClaw.
But a security runtime isn’t a deployment service. NemoClaw doesn’t configure your workflows. It doesn’t broker your credentials. It doesn’t manage your updates. It doesn’t vet your ClawHub skills. And it requires NVIDIA hardware that most cloud VPS deployments don’t have.
Better walls don’t build the house.
For founders and small teams deploying OpenClaw today, the practical question hasn’t changed: do you need a security component, or do you need a working, secured deployment? If you’re a DevOps-capable team with NVIDIA hardware and the time to write YAML policies, NemoClaw is worth evaluating as it matures past alpha. If you need your OpenClaw agent running securely by Friday on a cloud VPS — with email triage configured, credentials brokered, and someone patching the next CVE before it reaches your agent — that requires more than a runtime.
Frequently Asked Questions
Is NemoClaw free?
The software is free. The hardware isn’t. NemoClaw and OpenShell are open-source (Apache 2.0), but they require NVIDIA GPU hardware to run — GeForce RTX PCs/laptops, RTX PRO workstations, or DGX Spark/Station systems. If you’re running OpenClaw on a $12–$24/month cloud VPS (which most small businesses do), NemoClaw’s GPU requirements don’t apply to your setup. Think of it like getting free Tesla software updates — great deal, but only if you own the Tesla.
Does NemoClaw replace Docker sandboxing?
No — it layers on top of it. OpenShell’s kernel-level sandbox adds OS-enforced isolation beyond what Docker provides. Docker handles process namespacing and resource limits; OpenShell adds policy enforcement at the binary, destination, method, and path level. You still want the Docker hardening flags (non-root, cap-drop=ALL, read-only filesystem, no docker.sock) as your base layer. NemoClaw adds a second isolation boundary outside the container.
Can I use NemoClaw on a cloud VPS without a GPU?
Not practically. NemoClaw is designed for local deployment on NVIDIA GPU hardware. Cloud GPU instances (AWS G-series, GCP T4) might work but cost 10–20x more than a standard VPS. For cloud-hosted OpenClaw deployments, the 5-layer security stack — Docker hardening, DOCKER-USER firewall rules, Composio OAuth, tool allowlists, and system-level constraints — is the production-ready approach today.
Is NemoClaw production-ready?
Not yet. NVIDIA describes it as early-stage alpha. The r/LocalLLaMA community is already finding issues — WSL2 compatibility is broken, and workarounds are being PRed. NVIDIA is building toward production-ready sandbox orchestration, but the current focus is getting developer environments operational. If you need a production deployment this week, you need a solution that’s already stable.
What does the privacy router actually do?
It classifies each request and routes it based on your privacy and cost policies. Sensitive context (containing PII, confidential data, or proprietary information) stays on-device and is processed by local Nemotron models on your GPU. Non-sensitive requests go to frontier cloud models (Claude, GPT) for maximum capability. PII is stripped using differential privacy technology before anything reaches an external API. It’s genuinely useful for regulated industries — but it only works if you have NVIDIA hardware running locally.
Would NemoClaw have prevented the inbox-wipe incident?
Partially. OpenShell’s policy engine could restrict email access to read-only at the OS level, preventing deletion even if the agent’s internal instructions were overridden by context compaction. But NemoClaw wouldn’t have configured the read-only policy, set up system-level safety constraints, or brokered Gmail credentials through Composio OAuth with a kill switch. The inbox-wipe was a multi-layer failure. NemoClaw addresses 1 of those layers.