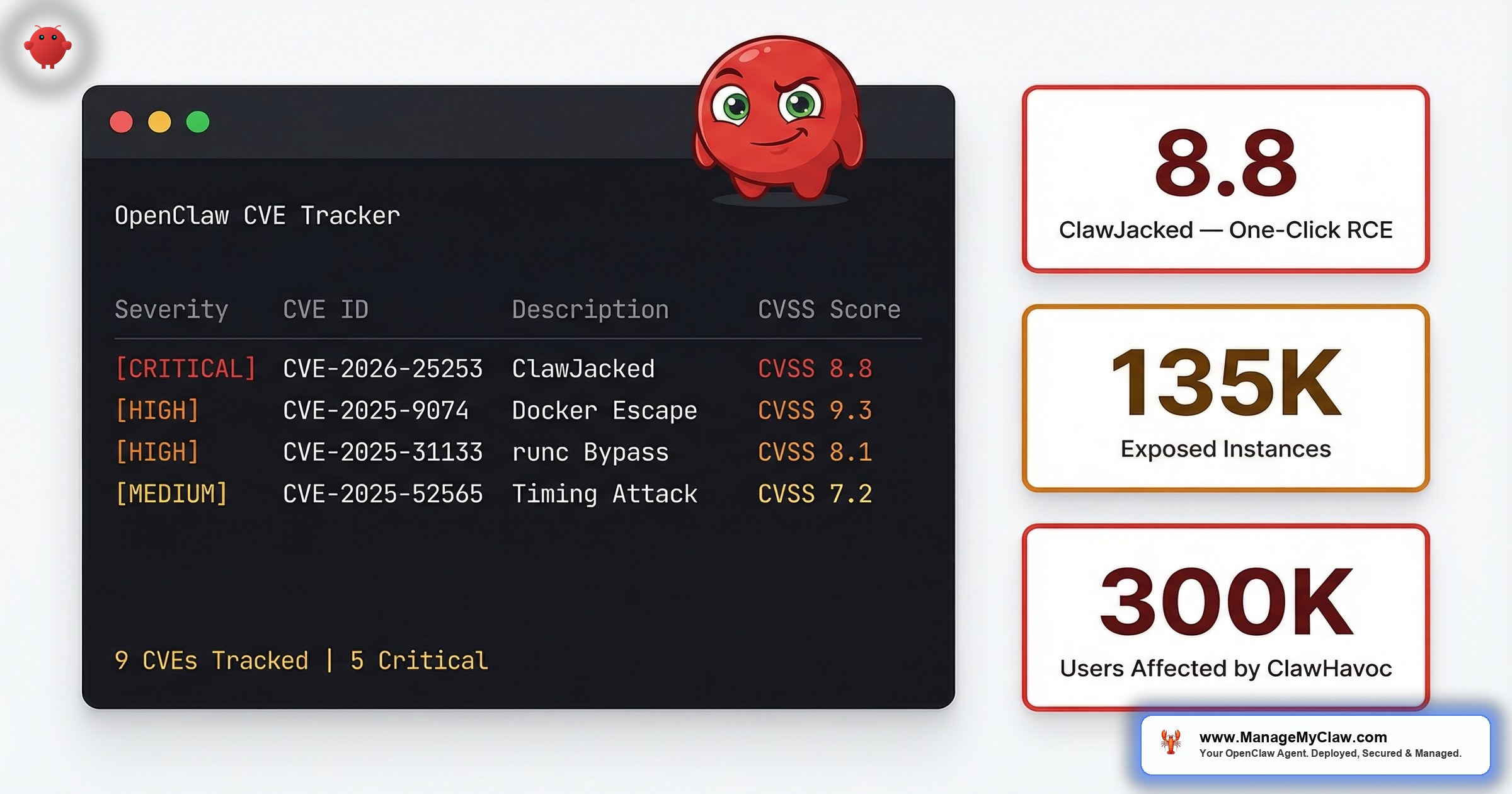
“9 disclosed CVEs. 17,500+ unpatched instances still reachable from the public internet. One CVSS 8.8 vulnerability that lets a website hijack your agent in under a second.”
That’s not a worst-case scenario. That’s the state of OpenClaw security as of March 2026, according to SecurityScorecard’s STRIKE team, who scanned 40,214 exposed OpenClaw instances and found 12,812 directly exploitable via remote code execution. Five security organizations — CNCERT, CrowdStrike, Cisco, Microsoft, and Belgium’s Centre for Cybersecurity — issued independent advisories about the same vulnerability in the same month. When five agencies all say “patch this now,” the subtext is: attackers are already here.
The patches exist. They’ve existed for weeks. The problem isn’t the software — it’s the 17,500+ deployments that haven’t applied them yet.
This tracker covers every OpenClaw CVE: the affected component, how the exploit actually works, the minimum version you need to be safe, and what each vulnerability means if you’re running a self-managed deployment. Bookmark it. Check your version. Then decide whether you want to keep tracking patches yourself or have someone do it for you.
Why CVE Tracking Matters More for AI Agents Than Anything Else You Run
A vulnerability in a misconfigured web server might expose a login form. A vulnerability in your AI agent exposes everything the agent can touch — your inbox, your calendar, your file system, your API credentials, and the tools that can execute shell commands on your host machine. The access footprint isn’t comparable.
“Think of it like the difference between someone breaking into your mailbox versus breaking into your house while you’ve left every drawer open and the car running in the garage. A compromised web server leaks data. A compromised AI agent takes actions.”
3 of OpenClaw’s 9 CVEs are remote code execution vulnerabilities. A 4th is an authentication bypass exploitable from your browser — no network access required. “I’ll update when it’s convenient” isn’t a maintenance posture for AI agent deployments. It’s a countdown.
And OpenClaw’s 9 CVEs aren’t outliers. They’re part of a systemic pattern. Between January and February 2026, security researchers filed over 30 CVEs targeting MCP servers, clients, and infrastructure — ranging from trivial path traversals to a CVSS 9.6 remote code execution flaw in a package downloaded 437,000 times. The OWASP Top 10 for Agentic Applications (2026), peer-reviewed by 100+ security researchers, now formally lists tool misuse, supply chain compromise, and unexpected code execution among its top risk categories.
On r/devsecops, a post titled “Scanned the official OpenClaw Docker image out of curiosity. 2,062 CVEs like WTF” hit 101 upvotes and 37 comments. The top comment: “Even the head of OpenClaw seems grossed out by how people are using it.” The container is more vulnerable than what’s inside it.
Why this matters: If you’re running OpenClaw on a VPS and you haven’t checked your version number this month, you don’t know whether your agent is patched. And with 5 national or major security organizations issuing warnings about the same platform in the same 30-day window, “I didn’t know” stopped being a defense a long time ago. The full security hardening framework covers everything beyond just version patching.
Understanding CVSS Scores (30-Second Primer)
Every CVE gets a CVSS score from 0.0 to 10.0. The score reflects attack complexity, whether credentials or network access are required, and the impact if exploitation succeeds. Here’s what the ranges mean for your deployment:
- 9.0–10.0 Critical: Remotely exploitable, no authentication, full system impact. Patch the same day you learn about it.
- 7.0–8.9 High: Serious attack vector with significant impact. Patch within days, not weeks.
- 4.0–6.9 Medium: Requires preconditions or has partial impact. Schedule in your next maintenance window.
- 0.1–3.9 Low: Limited exploitability or limited impact. Catch it in your normal release cycle.
OpenClaw’s 9 CVEs span medium to high, with 3 RCE vulnerabilities in the 7.1–7.3 band and the ClawJacked authentication bypass at 8.8. None are critical (9.0+). But 8.8 on a browser-exploitable bug that bypasses your firewall entirely is a meaningful threat by any measure.
The Full CVE Table
| CVE | CVSS | Type | Component | Status |
|---|---|---|---|---|
| CVE-2026-25253 “ClawJacked” | 8.8 | WebSocket auth bypass | Gateway | Patched (v3.1.8+) |
| CVE-2026-19847 | 7.3 | RCE via tool injection | Agent core | Patched (v3.0.4+) |
| CVE-2026-14521 | 7.1 | RCE via skill installer | Skill manager | Patched (v2.9.7+) |
| CVE-2026-11203 | 6.8 | RCE via memory write | Memory module | Patched (v2.8.2+) |
| CVE-2026-08441 | 6.2 | Privilege escalation | Docker config | Mitigated via config |
| CVE-2026-07133 | 5.9 | Privilege escalation | OAuth handler | Patched (v2.7.5+) |
| CVE-2026-04891 | 5.4 | Information disclosure | API logger | Patched (v2.6.9+) |
| CVE-2026-02217 | 4.8 | Information disclosure | Web UI | Patched (v2.6.1+) |
| CVE-2025-98431 | 4.3 | Denial of service | Gateway | Mitigated via config |
Two CVEs — CVE-2026-08441 and CVE-2025-98431 — are listed as “mitigated via config” rather than patched. The vulnerability exists in the code, but specific configuration controls prevent exploitation: Docker hardening flags for CVE-2026-08441, rate-limiting config for CVE-2025-98431. Both require the Docker sandboxing configuration to be applied correctly. If those controls aren’t in place, you’re vulnerable regardless of your OpenClaw version.
CVE-2026-25253 “ClawJacked”: The One That Triggered 5 Advisories
CVSS 8.8. WebSocket authentication bypass. Affects all versions before v3.1.8. Patched in v3.1.8+.
ClawJacked is the CVE that triggered the CNCERT advisory, the CrowdStrike advisory, the Cisco advisory, the Microsoft advisory, and the Belgian CCB advisory — all in March 2026. What makes it unusual isn’t just the CVSS score. It’s that it’s exploitable by anyone who can get you to visit a webpage, regardless of your firewall configuration.
How the Attack Works (The Full Chain)
Here’s what happens. You’re running OpenClaw on localhost. Your firewall is configured correctly. You feel safe. Then you visit a webpage — maybe a blog, a forum post, a link in an email. The page contains JavaScript that opens a WebSocket connection directly to your local OpenClaw gateway. OpenClaw’s gateway doesn’t validate the WebSocket Origin header — it accepts connections from any site, not just your own UI. The connection succeeds. The page exfiltrates your gateway token. The attacker registers as a trusted device. From that point, they can rewrite your tool policies, disable confirmation prompts, and set tools.exec.host to “gateway” — which routes commands to run directly on your host machine, outside the Docker container entirely.
Your firewall never sees this attack. It comes from your own browser. The CWE classification is CWE-669 (Incorrect Resource Transfer Between Spheres) — your browser acts as a bridge between an external malicious site and your locally-running agent, and the agent has no way to tell the difference.
Oasis Security’s analysis revealed an additional design flaw that made the exploit far more practical than the CVSS score alone suggests: the gateway’s rate limiter exempted localhost connections entirely. The malicious JavaScript could brute-force your gateway password at hundreds of attempts per second with no throttling. Combined with the missing Origin header validation, an attacker didn’t need to know your password in advance — the script cracked it live, in-browser, in seconds.
“Your firewall was locked. Your password was set. Your agent was on localhost. None of that mattered. The attack came through your browser like a guest walking through your front door and handing your house keys to a stranger standing behind them.”
How to Check if You’re Vulnerable
# Check your running OpenClaw version (direct install)
openclaw --version
# Check version inside Docker
docker exec openclaw-gateway openclaw --version
# Check image tag via Docker Compose
docker compose ps
# Look for the image tag on your openclaw-gateway service
# Patched version: v3.1.8 or later
# Anything before v3.1.8 is vulnerable to ClawJackedIf you’re running any version before v3.1.8 and OpenClaw has network access — even localhost-only — update before your next browser session, not your next maintenance window.
ClawJacked invalidated the most common security assumption in self-hosted deployments: “It’s on localhost, so it’s safe.” If you’ve been relying on network isolation as your primary defense, this CVE proved that model is broken for any software that communicates over WebSocket. The 5 security essentials guide covers the layered approach you need instead.
The 3 Remote Code Execution CVEs
Three CVEs in the 6.8–7.3 CVSS range give attackers the ability to execute arbitrary commands on your system. Each one targets a different component, and each has a different attack vector.
CVE-2026-19847: RCE via Tool Injection (CVSS 7.3)
Component: Agent core. Attack vector: Unsanitized input in tool calls reaches a code execution pathway. For deployments where the agent processes external content — emails, documents, web pages — the content itself becomes the injection vector. If your agent reads an email containing a crafted payload, the payload can execute commands. Fix: Patched in v3.0.4.
CVE-2026-14521: RCE via Skill Installer (CVSS 7.1)
Component: Skill manager. Attack vector: A malicious skill package exploits the installer at the binary level — code execution triggers during the install process itself, before the SKILL.md instructions even run. This is distinct from the ClawHavoc supply chain attack (which worked through AI instruction injection). This one doesn’t need the AI to cooperate. Fix: Patched in v2.9.7.
CVE-2026-11203: RCE via Memory Write (CVSS 6.8)
Component: Memory module. Attack vector: The component that manages SOUL.md and MEMORY.md persistent storage contains a write vulnerability that can trigger code execution. This is directly related to the attack vector used in the ClawHavoc campaign: malicious skills wrote to SOUL.md and MEMORY.md to establish persistence across sessions. CVE-2026-11203 closes the execution pathway. Fix: Patched in v2.8.2.
If you installed any ClawHub skills between November 2025 and February 2026, the memory-write RCE was the mechanism that gave malicious skills persistent access. Updating to v2.8.2+ closes the execution pathway, but it doesn’t undo damage from skills that already wrote to your memory files. Run openclaw skills list and verify every entry against a known-good source.
The 2 Privilege Escalation CVEs
CVE-2026-08441: Privilege Escalation via Docker Config (CVSS 6.2)
This CVE is “mitigated via config” rather than patched. The vulnerability exists in how Docker containers running OpenClaw can escalate privileges from the container user to the host. The fix isn’t a code patch — it’s specific Docker flags: --cap-drop=ALL, --security-opt no-new-privileges, and running as a non-root user (UID 1000+). Without these flags, a compromised container process can escalate to host-level access. This is why the security audit checklist treats Docker hardening flags as high-priority items.
CVE-2026-07133: Privilege Escalation via OAuth Handler (CVSS 5.9)
A logic flaw in OpenClaw’s OAuth handler allows certain API calls to execute at a higher permission level than the authenticating user should have. For multi-user deployments, this creates a lateral movement path. For single-user deployments, the practical impact is lower — but “lower” isn’t “none.” Patched in v2.7.5. If you’re using Composio for OAuth integrations, the Composio OAuth hardening guide covers additional configuration steps beyond this patch.
The 2 Information Disclosure CVEs
CVE-2026-04891: Information Disclosure via API Logger (CVSS 5.4)
OpenClaw’s API logger was writing credential-containing fields to log output. API tokens, OAuth headers, and in some configurations email content — all appearing in plain text in log files. If your logs are readable outside the container (mounted volumes, log forwarding services), this is a data exfiltration path. Patched in v2.6.9.
CVE-2026-02217: Information Disclosure via Web UI (CVSS 4.8)
The Web UI exposed internal state information — configuration values, connected integration metadata, session data — to any user with UI access, regardless of permission level. For single-user deployments, the impact is low. For team setups, one user can read another’s integration configuration. Patched in v2.6.1.
The Denial of Service CVE
CVE-2025-98431: DoS via Gateway (CVSS 4.3)
A malformed request crashes the gateway process. Your agent goes offline until it’s manually restarted. Mitigated via config — specifically, rate limiting on the gateway port. Without rate limiting, this becomes a trivial way to take your agent offline. For production deployments where your agent runs unattended workflows, repeated DoS attacks can disrupt scheduled tasks without leaving an obvious security footprint.
The ClawHavoc Context: CVEs Aren’t the Whole Picture
Patching CVEs handles code-level vulnerabilities. It doesn’t handle supply chain attacks. In January 2026, the ClawHavoc campaign placed 2,400+ malicious skills in ClawHub — OpenClaw’s official skill registry. At peak, 1 in 5 published skills was malicious. The payload was the AMOS infostealer, targeting SSH keys, browser credentials, and crypto wallets.
A post titled “Complete breakdown of every OpenClaw vulnerability — 6 CVEs, 341 malicious skills, 135K exposed instances, 1.5M leaked tokens” hit 196 upvotes. The top comment, with 54 upvotes: “Back in my days we publicly shamed those malware distributors. Now big tech give em a place to distribute shit at scale.. Funky times.”
“That’s what you get when you forget to add the ‘and make it secure’ bit in your prompt.”
— Top comment on r/selfhosted (103 upvotes), post with 150 upvotes on OpenClaw security incidents300,000 users were affected. The skills have since been removed, but ClawHub remains an open-upload registry without mandatory security review. Every skill you install is code running with your agent’s permissions.
“Downloading apps from a store where nobody checks for malware. That’s ClawHub today. The door is open, the bouncers are volunteers, and the line is 13,729 skills long.”
Patching your OpenClaw version addresses the 9 CVEs. It doesn’t address the skills already installed on your system. If you installed any ClawHub skill between November 2025 and February 2026, assume your SSH keys are compromised and rotate them now.
The Update Cadence Problem
OpenClaw shipped 7 updates in 2 weeks after the ClawJacked disclosure. That’s the right response to a CVSS 8.8 vulnerability — fast patching. But for self-managed deployments, each update is a manual operation: pull the new image, test that your skills still work, verify your Composio connections, confirm gateway token validity. 7 updates in 14 days means 7 manual update cycles, each one a potential source of configuration drift or workflow disruption.
Most self-installs don’t have a tested update process. They update when something breaks or when they happen to check GitHub. That gap — between when a patch ships and when it’s applied — is exactly the window attackers target after a CVE disclosure.
SecurityScorecard’s STRIKE team quantified the cost of that gap: of the 40,214 exposed OpenClaw instances they discovered, 12,812 were directly exploitable via remote code execution — meaning known, patched CVEs were still present and reachable on those deployments. The team also correlated 549 exposed instances with prior breach activity. These aren’t theoretical risks. They’re instances where the patch existed, the deployment didn’t apply it, and attackers found the gap before the operator did.
It’s like getting a recall notice for your car’s brakes, putting the letter in a drawer, and driving to work the next morning. The fix exists. The risk is choosing not to apply it. If you’re weighing self-management against a managed service, the ManageMyClaw vs DIY comparison breaks down exactly what ongoing maintenance involves.
Why this matters: If you’re self-managing your OpenClaw deployment, the question isn’t whether you can apply patches. It’s whether you have a process that guarantees you will — within 24 hours for critical CVEs, not “whenever I get around to it.” The full security hardening framework covers patch management as one layer of a defense-in-depth stack.
The Bottom Line
OpenClaw’s 9 CVEs are all patched or mitigatable. That’s the good news. The bad news is that “patched” and “applied” are very different words, and SecurityScorecard found 12,812 instances where nobody bothered to make them the same word. The CVEs span 3 remote code execution flaws, an authentication bypass that renders firewalls irrelevant, 2 privilege escalation paths, 2 information disclosure leaks, and a denial-of-service bug. The ClawHavoc supply chain attack operated alongside these CVEs, affecting 300,000 users through a separate vector entirely.
Every CVE on this list has a fix. Not every deployment has applied it.
OpenClaw is the most capable open-source AI agent available in 2026. That’s not in dispute. But running capable software without applying its security patches is like buying a vault and leaving the door open because the combination is written on a Post-it you haven’t read yet. The combination exists. The vault works. The question is whether you’ve done the 20 minutes of work that turns “running” into “secure.”
ManageMyClaw Managed Care patches critical CVEs (CVSS 7.0+) within 24 hours of release and moderate CVEs within 72 hours. Every patch is tested against a staging environment first. Starting at $299/month.
Frequently Asked Questions
How many CVEs does OpenClaw have right now?
9 disclosed CVEs as of March 2026. CVSS scores range from 4.3 to 8.8. That breaks down to 3 remote code execution, 1 WebSocket authentication bypass, 2 privilege escalation, 2 information disclosure, and 1 denial of service. All 9 are addressed in current releases — 7 via code patches, 2 via configuration mitigations that require you to apply the right Docker flags.
Wait — does running on localhost actually protect me from ClawJacked?
No. That’s exactly what makes ClawJacked unusual. It’s exploitable even with OpenClaw bound to localhost and your firewall correctly configured. The attack routes through your browser, not your network. A malicious webpage opens a WebSocket to localhost, brute-forces your gateway password at hundreds of attempts per second (no rate limiting on local connections), and registers as a trusted device. The only fix is updating to v3.1.8+. Localhost isn’t a security boundary when your browser is the attack vector.
What does “mitigated via config” actually mean?
It means the vulnerability isn’t patched in the code — it’s blocked by configuration controls you have to apply yourself. CVE-2026-08441 (privilege escalation) requires Docker flags: --cap-drop=ALL, --security-opt no-new-privileges, and running as UID 1000+. CVE-2025-98431 (DoS) requires rate limiting on the gateway port. If those controls aren’t in place, you’re vulnerable regardless of your OpenClaw version. Most DIY setups skip these flags. The Docker sandboxing guide walks through every required flag.
Why did 5 security organizations issue warnings about the same vulnerability?
CNCERT, CrowdStrike, Cisco, Microsoft, and Belgium’s CCB each published independent advisories about CVE-2026-25253 in March 2026. When that many agencies issue separate warnings about the same platform, the vulnerability is either actively exploited, imminent, or both. For ClawJacked, it was both — the exploit chain was publicly documented and trivial to reproduce, with no authentication required beyond what the brute-force script handles automatically.
How fast does ManageMyClaw apply patches?
Critical CVEs (CVSS 7.0+) within 24 hours. Moderate CVEs within 72 hours. Every patch is staged and tested before deploying to production instances — the 24-hour window includes verification, not just pulling a new image. The ClawJacked patch shipped to Managed Care clients the same day it was released, after staging confirmed no workflow breakage. That’s the Managed Care SLA, starting at $299/month.