22+ CVEs in under 60 days. The security model got patched. Then the patches got bypassed.
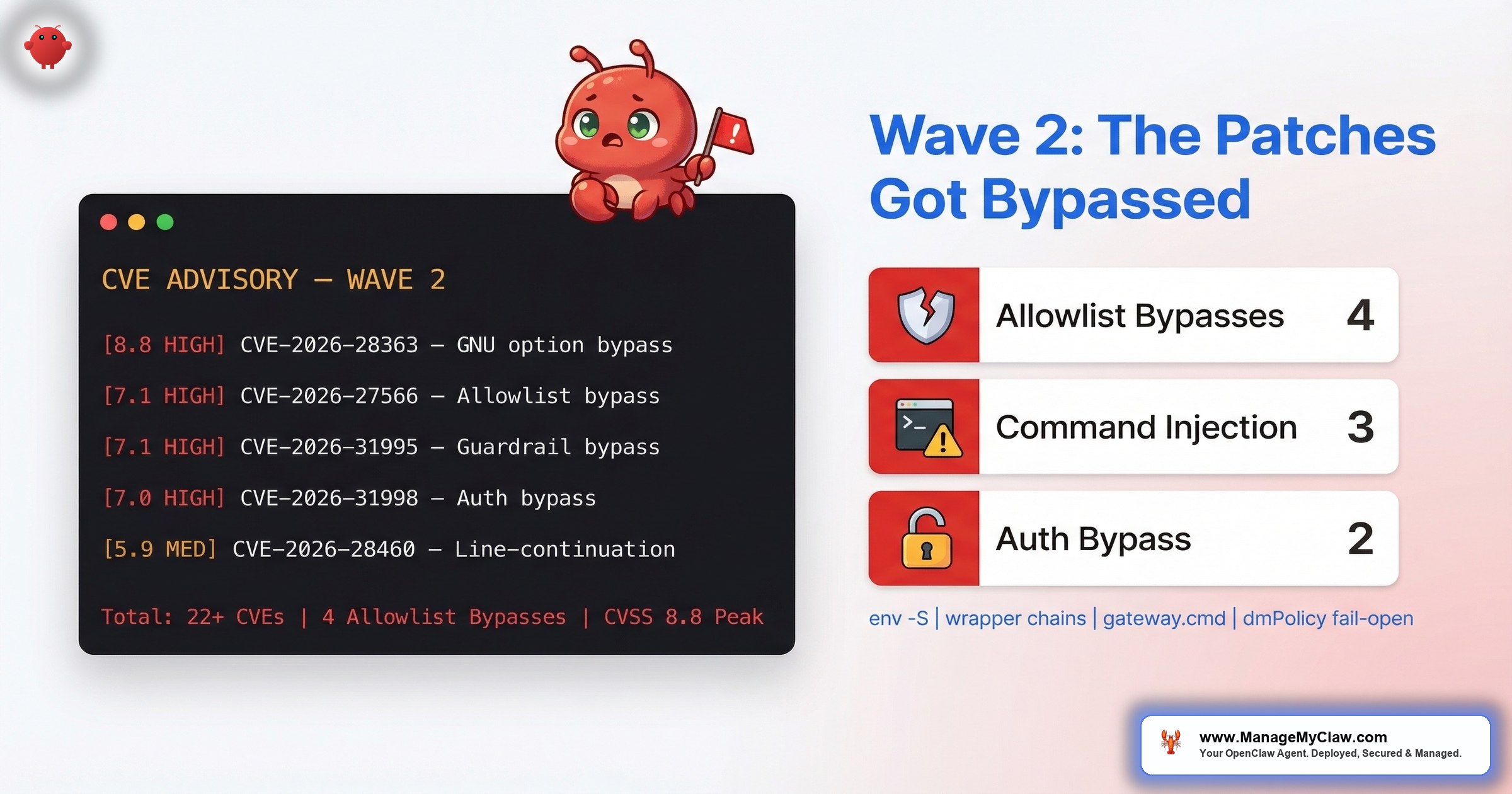
22+ CVEs. That’s how many disclosed vulnerabilities OpenClaw now carries — 9 from the first wave we documented in our CVE tracker, and 13+ more filed since February 2026. The first batch gave us a CVSS 8.8 authentication bypass and 3 remote code execution flaws. This second wave matches that high-water mark: CVE-2026-28363, a GNU long-option abbreviation bypass, scores CVSS 8.8 — the same severity as the original ClawJacked vulnerability. Beyond that headline number, the wave reveals a deeper pattern: allowlist bypasses that undermine the very guardrails OpenClaw added to fix the first round of problems.
On r/netsec, a post titled “We audited 1,620 OpenClaw skills — safety scanner labels 91% of confirmed threats benign” hit 75 points and 8 comments. That stat sits alongside SecurityScorecard’s STRIKE team finding 12,812 directly exploitable instances out of 40,214 scanned, and the broader trend of over 30 CVEs targeting MCP servers filed in the first 60 days of 2026. OpenClaw’s vulnerability count isn’t an outlier — it’s tracking with the infrastructure category it belongs to.
This post covers each of the 13+ new CVEs: what they target, how they work, and the minimum version that fixes them. If you’ve already read the original CVE tracker, consider this the sequel nobody wanted.
Allowlist Bypasses Are the New Attack Surface
The first 9 CVEs targeted OpenClaw’s core — the gateway, the agent runtime, the skill installer, the memory module. The fixes added guardrails: allowlists for approved commands, policy checks for tool execution, approval flows for sensitive operations. Those defenses work when they can’t be circumvented.
6 of the 13+ new CVEs are allowlist or authorization bypasses. Attackers aren’t breaking through the wall anymore. They’re walking around it.
It’s the security equivalent of installing a deadbolt on your front door, then discovering the attackers are coming through the dog flap. The lock works perfectly. The perimeter doesn’t.
This matters because allowlists are how most teams configure OpenClaw in production. You define which binaries your agent can run, which commands are approved, and which skills are trusted. If those allowlists can be bypassed by wrapping commands in env bash or persisting wrapper-level entries, your production security posture is weaker than you think it is.
13+ New CVEs at a Glance
| CVE | CVSS | Type | Component | Fixed In |
|---|---|---|---|---|
| CVE-2026-28363 | 8.8 | Allowlist bypass | GNU long-option abbreviation (sort command) | TBD |
| CVE-2026-27566 | 7.1 | Allowlist bypass (CWE-78) | system.run exec analysis | 2026.2.22 |
| CVE-2026-31995 | 7.1 | Allowlist bypass | system.run guardrails | 2026.2.22 |
| CVE-2026-31992 | 7.1 | Authorization bypass | Allow-always wrapper persistence | 2026.2.22 |
| CVE-2026-31998 | 7.0 / 8.3 (v4) | Authorization bypass | Synology-chat channel plugin | 2026.2.24 |
| CVE-2026-31994 | — | Command injection (Priority 1) | Windows scheduled task (cmd metachar) | 2026.2.19 |
| CVE-2026-22176 | — | Command injection | Windows scheduled task (unquoted set) | 2026.2.19 |
| CVE-2026-32000 | — | Command injection | Lobster extension shell fallback (shell:true) | TBD |
| CVE-2026-28461 | — | Denial of service | Zalo webhook memory exhaustion | 2026.3.1 |
| CVE-2026-28478 | — | Denial of service | Unbounded webhook body buffering | 2026.2.13 |
| CVE-2026-28460 | 5.9 | Allowlist bypass | Shell line-continuation in system.run | TBD |
| CVE-2026-32059 | — | Command execution bypass | Sort command execution bypass | TBD |
| CVE-2026-29607 | — | Details pending | — | TBD |
CVE-2026-29607 has been assigned and flagged by RedPacket Security but doesn’t yet have a full technical disclosure. We’ll update this post when details are published. Community tracking is available at github.com/jgamblin/OpenClawCVEs, a maintained OpenClaw CVE repository.
Sources: VulnCheck advisories, GitLab Advisory Database, GitHub Security Advisory GHSA-gw85-xp4q-5gp9, DailyCVE.com, CVEReports.com, RedPacket Security, Particula.tech.
The Critical Allowlist Bypass: CVE-2026-28363
This is the highest-severity CVE in the entire second wave — matching the original ClawJacked score.
CVE-2026-28363: GNU Long-Option Abbreviation Bypass
OpenClaw’s allowlist mode validates command names against a list of approved binaries. But it doesn’t account for GNU long-option abbreviation behavior. GNU coreutils allow users to abbreviate long options as long as the abbreviation is unambiguous — and attackers exploit this to bypass validation on the sort command. The allowlist sees a permissible option string. GNU parses the abbreviation and executes the full command with the intended (malicious) behavior.
At CVSS 8.8, this vulnerability is classified as HIGH severity with high impact across confidentiality, integrity, and availability. It’s the kind of flaw that exploits a fundamental assumption in the security model: that the command string the policy engine evaluates is the same command string the operating system executes. When GNU option expansion sits between those two layers, they’re not the same string at all.
Imagine a bouncer checking IDs against a guest list, but guests can abbreviate their names and the bouncer accepts “J. Sm” as matching “John Smith.” The verification passes. The person walking in might not be John Smith.
The Allowlist Bypasses
Beyond CVE-2026-28363, 4 more CVEs share a common theme: OpenClaw’s command execution policy can be tricked by wrapping blocked commands inside approved binaries, using line-continuation characters, or exploiting option-parsing quirks. The allowlist checks the outer command. The inner payload runs unchecked.
CVE-2026-27566: Env and Shell-Dispatch Wrapper Chains
OpenClaw’s system.run exec analysis validates commands against an allowlist before execution. But the analysis fails to unwrap environment and shell-dispatch wrapper chains. An attacker routes a payload through wrapper binaries like env bash — the allowlist sees env (approved), not the bash command it dispatches to. The payload runs with full agent permissions.
CVSS 7.1 | CWE-78 (OS Command Injection) | High integrity-impact. Exposed deployments running as a service or worker processing requests from external systems, CI jobs, or automation pipelines are at highest risk. If your agent accepts input from upstream systems — webhooks, CI runners, queued jobs — this is the one to patch first.
Affected versions: All versions before 2026.2.22.
CVE-2026-31995: The env -S Guardrail Bypass
A variation on the same theme but targeting a different code path. When /usr/bin/env is allowlisted — which it is in most default configurations — attackers use env -S to split and execute arbitrary command strings that bypass the policy analysis entirely. The -S flag tells env to split a single string into multiple arguments and execute them. OpenClaw’s guardrails don’t parse that split.
Think of it as an airport security scanner that checks your bag but doesn’t open the bag inside your bag. The outer container passes inspection. The inner one carries what it wants.
Affected versions: All versions before 2026.2.22.
CVE-2026-31992: Allow-Always Wrapper Persistence
This one is architecturally distinct from the other two. Instead of bypassing the allowlist at execution time, it persists wrapper-level allowlist entries that bypass approval checks permanently. Once a wrapper-level entry is persisted, the agent no longer prompts for approval on that command path. An attacker who gets one malicious entry into the wrapper allowlist has a persistent, silent execution channel that survives restarts.
Unlike other bypasses, this one leaves behind artifacts. Even after patching, malicious allowlist entries from pre-patch exploitation could still be in your configuration.
Affected versions: All versions before 2026.2.22.
CVE-2026-28460: Shell Line-Continuation Bypass (CVSS 5.9)
A distinct bypass path targeting system.run in allowlist mode. Attackers use shell line-continuation characters (backslash-newline sequences) to split a blocked command across multiple lines. The allowlist parser sees the first fragment — which looks innocuous — and approves it. The shell reassembles the full command at execution time and runs it. At CVSS 5.9 (MEDIUM), the complexity is higher than the wrapper-chain bypasses, but the impact is the same: arbitrary command execution past the policy layer.
CVE-2026-32059: Sort Command Execution Bypass
Reported by TheHackerWire, this CVE targets the sort command execution path — closely related to CVE-2026-28363’s GNU option abbreviation vector but exploiting a different code path in the execution pipeline. The sort binary is commonly allowlisted because it’s considered a safe data-processing utility. These two CVEs together demonstrate that even “safe” binaries can become attack vectors when their option-parsing behavior diverges from what the policy engine expects.
If you’re relying on OpenClaw’s command allowlists as your primary security control — which is how most production deployments work — these 5 CVEs (plus the CVSS 8.8 GNU abbreviation bypass above) collectively mean your allowlist was bypassable through multiple paths. The wrapper-chain and env -S bypasses were fixed in 2026.2.22. The GNU abbreviation and line-continuation bypasses represent newer attack research on the same surface. The security audit checklist covers how to verify your allowlist configuration is actually enforcing what you think it’s enforcing.
The Authorization Bypass (1 CVE)
CVE-2026-31998: Synology-Chat Channel Plugin Fails Open
The Synology-chat channel plugin has a configuration flaw where setting dmPolicy to allowlist with an empty allowedUserIds array fails open instead of closed. Instead of blocking all users (the expected behavior of an empty allowlist), it permits everyone. Any user can trigger unauthorized agent dispatch through the channel integration.
The root cause is specific: the checkUserAllowed function incorrectly treated an empty user allowlist as a permissive “allow-all” rule when dmPolicy was set to allowlist. This function is called by createWebhookHandler, which is the entry point for all incoming Synology Chat messages. Tracked as GHSA-gw85-xp4q-5gp9.
This is a textbook “fail-open vs. fail-closed” design error. An empty allowlist should mean “nobody is allowed.” In this implementation, it means “everybody is allowed.” If you’re running the Synology-chat integration and haven’t explicitly populated the user ID list, your agent is responding to commands from any user on the Synology chat instance.
CVSS v3.1: 7.0 (HIGH) | CVSS v4.0: 8.3. The v4 score reflects the direct webhook attack surface and the fact that no authentication is required to exploit it.
Affected versions: All versions before 2026.2.24. (Correction: the original version of this post stated 2026.2.22. The actual patched version is 2026.2.24.)
The Windows Command Injections (2 CVEs)
Both of these target OpenClaw’s Windows scheduled task script generation. If you’re running OpenClaw on Linux or in Docker (the majority of deployments), these don’t directly affect you. If you’re on Windows — or if your agent generates scheduled tasks for Windows endpoints — they do.
CVE-2026-31994: CMD Metacharacter Injection
OpenClaw generates gateway.cmd files for Windows scheduled tasks. The generation process doesn’t sanitize cmd metacharacters. An attacker who controls any input that flows into the scheduled task name, path, or parameters can inject arbitrary commands that execute when the task runs. Local command injection — requiring local access or control of upstream data, but no authentication bypass needed. Metacharacter-only values or CR/LF sequences are sufficient to execute unintended code.
Build agents, CI runners, and automation servers are the most exposed deployment profiles. If your Windows-based agent processes any externally-sourced input, this is actively exploitable.
Affected versions: All versions before 2026.2.19.
CVE-2026-22176: Unquoted Environment Variable Assignment
A related but distinct injection path. Environment variables are written to gateway.cmd using unquoted set KEY=VALUE assignments. If the value contains cmd metacharacters, they’re interpreted as commands. A value like normal_value & malicious_command executes both the assignment and the injected command. The dangerous metacharacters include &, |, ^, %, and ! — any of which can break out of the assignment context and into command execution.
Same house, different window. Two paths to the same result: arbitrary code execution through your scheduled task infrastructure.
Affected versions: All versions before 2026.2.19.
The Command Injection via Shell Fallback (1 CVE)
CVE-2026-32000: Lobster Extension Tool Execution with Windows Shell Fallback
(Correction: the original version of this post attributed CVE-2026-32000 to the Zalo webhook endpoint. The Zalo webhook memory exhaustion is actually CVE-2026-28461 (see below). CVE-2026-32000 targets the Lobster extension tool execution path.)
The Lobster extension’s tool execution layer uses a Windows shell fallback mechanism: when a subprocess launch fails with EINVAL or ENOENT errors, the code retries the execution with shell: true. That fallback path doesn’t sanitize the command arguments. An attacker injects shell metacharacters into the tool invocation parameters, knowing the initial spawn will fail and the retry will hand the unsanitized payload to cmd.exe.
It’s a two-step exploit: force the safe path to fail, then ride the unsafe fallback. The code handles the error. The error handler is the vulnerability.
The Denial of Service Flaws (2 CVEs)
CVE-2026-28461: Zalo Webhook Memory Exhaustion
The Zalo webhook endpoint doesn’t bound memory allocation for incoming requests. A remote attacker sends repeated requests with different query parameters, each one allocating memory that’s never freed. Enough requests and the process hits OOM — your agent crashes, your workflows stop, and everything stays down until you manually restart.
If you’re running the Zalo integration and haven’t updated past March, this one is live on your deployment right now.
Affected versions: All versions before 2026.3.1.
CVE-2026-28478: Unbounded Webhook Request Body Buffering
A broader variant of the same class of flaw. OpenClaw’s webhook handlers buffer incoming request bodies without enforcing strict byte or time limits. Remote unauthenticated attackers send oversized JSON payloads to any webhook endpoint, and the handler dutifully reads the entire body into memory. No authentication required. No rate limiting. Just a POST request with a multi-gigabyte body.
While CVE-2026-28461 targets the Zalo integration specifically, this CVE affects webhook handlers more broadly. If you expose any webhook endpoint to the internet — which is how most channel integrations work — you’re exposed.
Affected versions: All versions before 2026.2.13.
The Pending Disclosure (1 CVE)
CVE-2026-29607 has been assigned a CVE number and flagged by RedPacket Security, but full technical details haven’t been published yet. It could be minor. It could be critical. Without disclosure, you can’t assess risk — which is itself a risk if you’re self-managing. We’ll update this post and the main CVE tracker when details are available.
22+ CVEs in Under 60 Days
Here’s the full timeline in context:
- January 25, 2026: OpenClaw launches.
- January–February: First 9 CVEs disclosed (CVSS 4.3–8.8), including the ClawJacked authentication bypass. 5 security organizations issue advisories.
- February–March: 13+ more CVEs filed. A CVSS 8.8 GNU long-option abbreviation bypass matches the original ClawJacked score. Allowlist bypasses dominate. Windows deployments get 2 command injection flaws plus a shell-fallback exploit. The broader MCP ecosystem crosses 30 disclosed CVEs. Particula.tech reports “20% of OpenClaw skills were found malicious” after the project hit 250K GitHub stars.
- March 2026: AWS launches managed OpenClaw on Lightsail. NVIDIA ships NemoClaw. The market response to the security problem is accelerating faster than the security problem itself.
On r/cybersecurity, a post titled “Complete breakdown of every OpenClaw vulnerability” hit 197 points and 11 comments. On r/devsecops, “Scanned the official OpenClaw Docker image — 2,062 CVEs like WTF” hit 101 upvotes. The community isn’t surprised by new CVEs anymore. They’re tracking them the way you track weather during hurricane season.
What This Wave Tells You About Self-Managed Risk
The first 9 CVEs taught one lesson: patch fast. This second wave of 13+ teaches a different one: patching isn’t enough if you don’t understand what changed.
Consider the allowlist bypass cluster. If you updated to 2026.2.22, you’re patched. But do you know whether your allowlist was exploited before you patched? CVE-2026-31992 persists wrapper-level entries that survive restarts. If an attacker used that window, the malicious entry is still in your configuration after you update. The patch prevents new bypasses. It doesn’t clean up old ones.
That’s the difference between updating software and maintaining a security posture. The first is a version number. The second is a process — one that includes post-patch auditing, allowlist review, and log analysis. The Docker sandboxing guide covers the container-level controls that limit blast radius even when application-level guardrails are bypassed.
Updating your locks after a break-in is necessary. Checking whether anyone made a copy of the key first is the part people skip.
Are You Covered?
Here’s the minimum version you need to be safe against the fully disclosed CVEs in this wave with known fix versions:
| If you’re on version… | You’re exposed to… | Action |
|---|---|---|
| Before 2026.2.13 | All disclosed CVEs including webhook body buffering DoS | Update immediately |
| 2026.2.13–2026.2.18 | Windows cmd injections + allowlist/auth bypasses + Zalo DoS | Update to 2026.3.1+ |
| 2026.2.19–2026.2.23 | Allowlist/auth bypasses + Synology-chat (fix: 2026.2.24) + Zalo DoS | Update to 2026.3.1+ |
| 2026.2.24–2026.2.28 | Zalo webhook DoS only | Update to 2026.3.1+ |
| 2026.3.1+ | GNU option bypass (8.8), shell line-continuation (5.9), Lobster shell fallback, sort bypass, + 1 pending | Audit allowlist config + monitor for patches |
The safe floor is version 2026.3.1 for known patched CVEs. But 5 CVEs in this wave (CVE-2026-28363, CVE-2026-28460, CVE-2026-32000, CVE-2026-32059, and CVE-2026-29607) don’t yet have confirmed fix versions. The safe floor will move again. Track updates at github.com/jgamblin/OpenClawCVEs.
The Bottom Line
OpenClaw now has 22+ disclosed CVEs in under 60 days of existence. The first 9 targeted core infrastructure. The second 13+ target the guardrails that were added to fix the first 9 — and one of them, CVE-2026-28363, matches the original ClawJacked CVSS 8.8 severity. That’s not a failure of patching speed — OpenClaw’s maintainers are shipping fixes within days. It’s a reflection of what happens when a project with 250,000+ GitHub stars and deep system access gets the full attention of the security research community.
If you’re self-managing, the question isn’t whether you can keep up with one CVE. It’s whether you can keep up with 22+ and counting — including post-patch configuration audits, allowlist reviews, and monitoring for CVEs that don’t even have fix versions yet. That’s not a version number problem. That’s an operational capacity problem.
ManageMyClaw Managed Care patches critical CVEs within 24 hours of release, conducts post-patch allowlist audits, and monitors for new advisories including the pending disclosures. Starting at $299/month — less than the cost of one incident response engagement.
Frequently Asked Questions
How many total CVEs does OpenClaw have now?
22+ disclosed CVEs as of March 2026. The first 9 (CVSS 4.3–8.8) were filed between January and February 2026, covering remote code execution, authentication bypass, privilege escalation, information disclosure, and denial of service. The second batch of 13+, disclosed since February, adds a CVSS 8.8 GNU long-option abbreviation bypass, multiple allowlist bypasses, command injections on Windows, an authorization bypass in the Synology-chat plugin, a shell-fallback exploit in the Lobster extension, two denial-of-service flaws targeting webhook endpoints, and 1 CVE with details still pending.
What are the allowlist bypass CVEs and why do they matter?
Six CVEs target OpenClaw’s command execution allowlists — the primary mechanism most deployments use to restrict what an agent can run. CVE-2026-28363 (CVSS 8.8, the highest in this wave) exploits GNU long-option abbreviations to bypass the sort command. CVE-2026-27566, CVE-2026-31995, and CVE-2026-31992 wrap blocked commands inside approved binaries (like env bash or env -S) to smuggle payloads past the policy analysis. CVE-2026-28460 uses shell line-continuation characters. CVE-2026-32059 targets the sort command execution path. The wrapper-chain bypasses are fixed in 2026.2.22; others are awaiting patches.
Do the Windows command injection CVEs affect Linux/Docker deployments?
CVE-2026-31994 and CVE-2026-22176 specifically target Windows scheduled task script generation in gateway.cmd files. If you’re running OpenClaw exclusively on Linux or in Docker containers, these don’t directly affect your deployment. However, if your agent generates scheduled tasks for Windows endpoints or if any part of your workflow chain touches Windows, you should update to version 2026.2.19 or later.
What’s the minimum safe version for all known CVEs?
Version 2026.3.1 covers all CVEs from this wave that have published fix versions. Combined with the patches from the first wave, you need at least version 2026.3.1 to be covered against all patched CVEs. However, 5 CVEs in this wave (CVE-2026-28363, CVE-2026-28460, CVE-2026-32000, CVE-2026-32059, and CVE-2026-29607) don’t have confirmed fix versions yet. The safe floor will move when those patches land.
Is updating enough, or do I need to audit my configuration too?
Updating patches the vulnerability. It doesn’t undo exploitation that may have occurred before you patched. CVE-2026-31992 specifically persists wrapper-level allowlist entries that survive restarts. If your deployment was exposed before the update, malicious allowlist entries could still be in your configuration. After updating, review your allowlist configuration, check for unexpected persistent entries, and audit logs for unusual command execution patterns.
Why is there still a CVE with no details?
CVE-2026-29607 has been assigned a CVE number and flagged by RedPacket Security, but the full technical disclosure hasn’t been published. This is standard practice — CVE numbers are often reserved before details are made public, sometimes to give vendors time to patch. Until details are published, you can’t assess whether your deployment is affected or what mitigation steps to take. (Update: CVE-2026-28461, previously listed as pending, has been confirmed as the Zalo webhook memory exhaustion flaw affecting versions before 2026.3.1.)
How does ManageMyClaw handle this volume of CVEs?
ManageMyClaw Managed Care ($299/month) monitors all disclosed and pending CVEs, patches critical vulnerabilities within 24 hours of release, and conducts post-patch configuration audits including allowlist review. For the pending CVEs and the 5 awaiting fix versions, Managed Care clients are automatically covered when patches are published — no manual tracking required.